Trojan:O97M/Madeba!pz is a type of malicious software, commonly known as a Trojan, that targets Microsoft Office documents. Specifically, it affects files created with older versions of Microsoft Office, such as Office 97-2003 (.doc, .xls, .ppt files).
Trojans like Madeba!pz typically work by exploiting vulnerabilities in the Office suite to execute malicious code when the infected document is opened. Once activated, they may perform various harmful actions, such as stealing sensitive information, compromising system security, or installing additional malware on the infected computer.
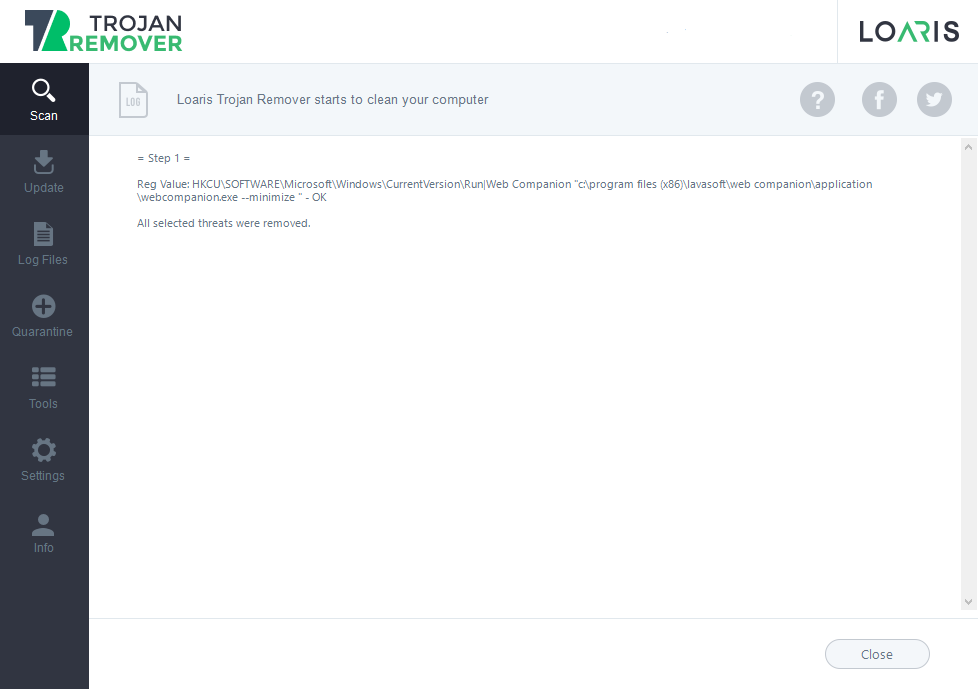
Trojan:Win32/Casdet!rfn in Action

Trojan:O97M/Madeba!pz can be injected into a Windows PC through various methods, primarily exploiting vulnerabilities in software or through social engineering tactics. Here’s an analysis of potential ways it could infect your system:
- Email Attachments: One common method is through malicious email attachments. Attackers might send emails pretending to be from legitimate sources, such as a colleague, friend, or trusted organization. These emails often contain attachments that appear harmless, such as Word documents, Excel spreadsheets, or PowerPoint presentations. However, these files contain malicious macros or scripts that, when executed, download and execute the Trojan on your system.
- Drive-By Downloads: Another method involves drive-by downloads, where the Trojan is silently downloaded and installed on your system when you visit a compromised or malicious website. These websites exploit vulnerabilities in your browser or browser plugins to execute malicious code without your knowledge.
- Infected External Devices: Trojan:O97M/Madeba!pz can also spread through infected external devices such as USB drives, external hard drives, or even smartphones. When you connect an infected device to your PC, the Trojan may automatically execute and infect your system.
- Exploiting Software Vulnerabilities: Trojan:O97M/Madeba!pz often exploits vulnerabilities in software applications to gain unauthorized access to your system. This could include vulnerabilities in Microsoft Office, web browsers, or other commonly used software. Attackers exploit these vulnerabilities by crafting specially designed documents or files that, when opened, trigger the execution of malicious code.
- Social Engineering: Attackers may use social engineering tactics to trick you into manually downloading and executing the Trojan. For example, they might create fake websites or advertisements that claim to offer free software, games, or media content. When you download and run these files, you inadvertently install the Trojan on your system.
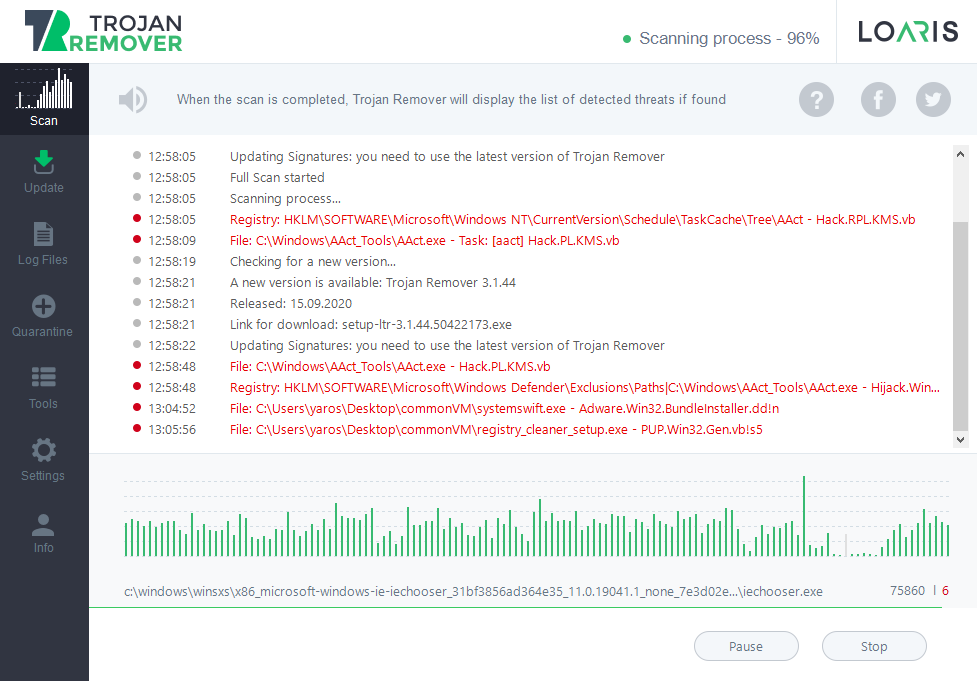
Trojan:O97M/Madeba!pz is delivered to the victim’s system through one of the methods mentioned earlier, such as email attachments, drive-by downloads, infected external devices, or exploiting software vulnerabilities.
Once the malicious file is opened or executed, the Trojan’s code is activated. This could involve exploiting vulnerabilities in software applications, executing malicious macros in Microsoft Office documents, or leveraging other means to execute its payload.
Trojan Madeba persistence on the infected system to ensure it remains active even after the system reboots. It may achieve this by creating registry entries, modifying system files, or installing itself as a service or startup program.
After establishing persistence, the Trojan executes its payload. This payload could include various malicious activities, such as stealing sensitive information, logging keystrokes, capturing screenshots, encrypting files for ransom, or turning the infected system into a bot for use in a botnet.
It may attempt to communicate with remote command-and-control (C&C) servers operated by the attackers. This communication allows the attackers to send commands to the infected system, retrieve stolen data, or update the Trojan with new instructions or payloads.
Trojan:O97M/Madeba!pz employs evasion techniques to avoid detection by antivirus or security software. This could include polymorphic code that changes its appearance with each infection, obfuscation techniques to conceal its true purpose, or anti-analysis measures to thwart reverse engineering attempts.
Trojan:O97M/Madeba!pz can spread to other systems on the network or via removable drives. They attempt to exploit vulnerabilities in network services or use social engineering tactics to trick users on the same network into executing the malware. It deletes logs, modifies system files, or otherwise attempts to hide its presence on the infected system.
Trojan:O97M/Madeba!pz Summary
Trojan:Win32/Casdet!rfn employs sophisticated techniques to evade detection and analysis. These include: