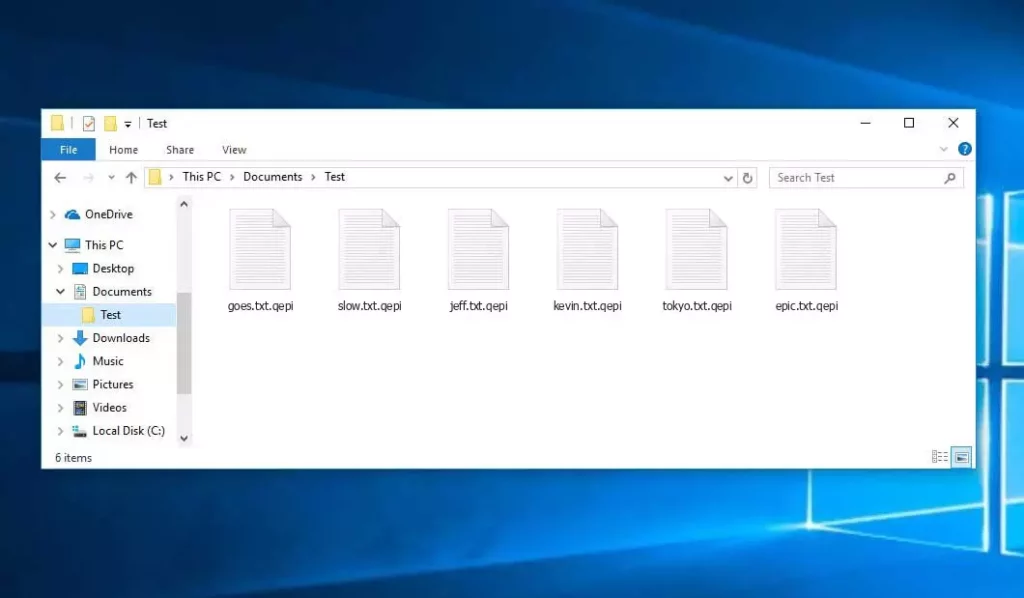
The Qepi virus belongs to the STOP/Djvu ransomware group and targets Windows computers. It works by encrypting the files on these computers, changing them into files with a “.Qepi” extension, and then leaving a ransom note named “readme.txt” in each folder it affects.
Known as one of the most powerful types of malware, the Qepi virus successfully blocks many different ways that might be used to recover encrypted files.
In this post, I’ll walk you through the events following a Qepi virus attack and guide you on removing the malware from your system. You’ll also discover multiple file recovery methods post-attack.
Understanding the Qepi Virus
The Qepi ransomware, a malicious software targeting user files, encrypts them using a robust Salsa20 cipher, incapacitates antivirus programs, and erases backups. It modifies every document – whether a Word file, Excel spreadsheet, or photo – by appending a Qepi file extension. For instance, “photo.jpg” becomes “photo.jpg.qepi”. It then creates a ransom note called _readme.txt and places it in each folder containing encrypted files on your desktop, which details the ransom payment instructions as follows:
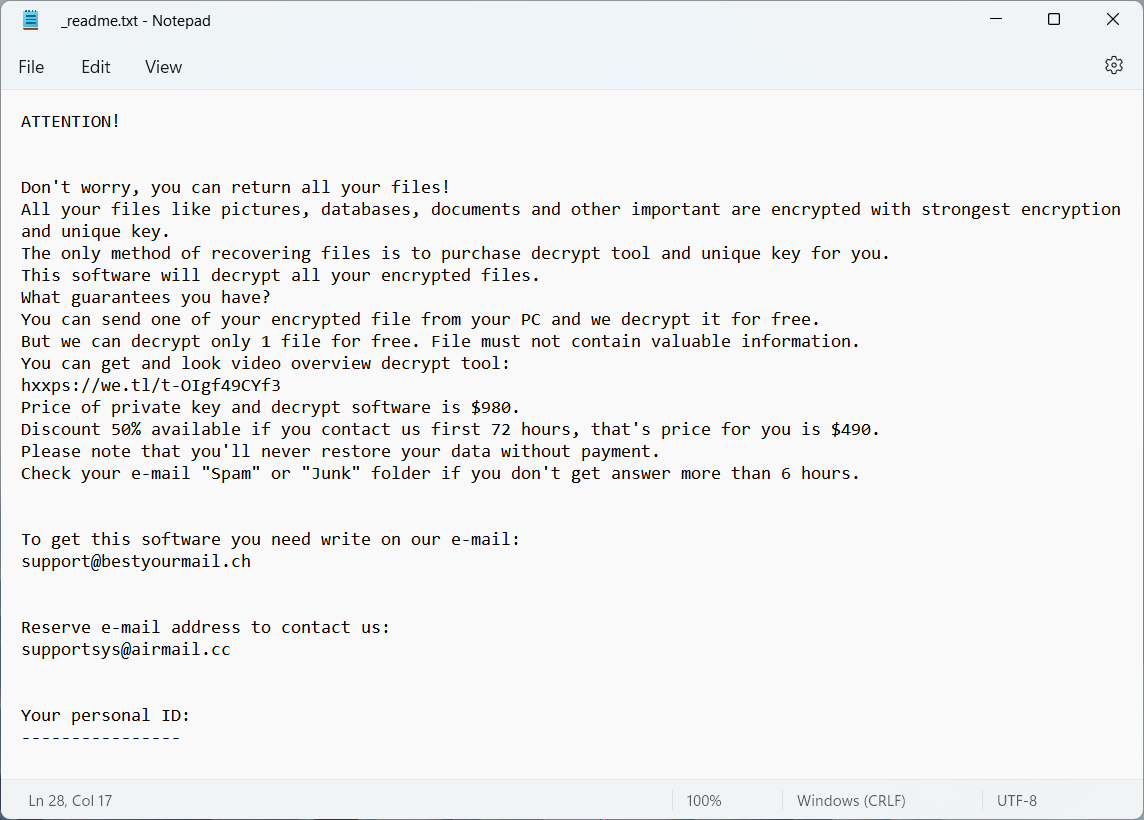
ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents, and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
Do not ask assistants from youtube and recovery data sites for help in recovering your data.
They can use your free decryption quota and scam you.
Our contact is emails in this text document only.
You can get and look video overview decrypt tool:
https://we.tl/t-hPAqznkJKD
Price of private key and decrypt software is $999.
Discount 50% available if you contact us first 72 hours, that's price for you is $499.
Please note that you'll never restore your data without payment.
Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours.
To get this software you need write on our e-mail:
support@freshingmail.top
Reserve e-mail address to contact us:
datarestorehelpyou@airmail.cc
Your personal ID:
Sharing habits with most STOP/Djvu ransomware variants, the Qepi ransomware represents over 70% of individual ransomware attacks since its 2018 inception. It introduced many features now common across ransomware targeting individuals, such as ransom demands, notification methods, and backup prevention measures.
Qepi Ransomware
STOP/Djvu ransomware, including the Qepi variant, spreads through similar channels, namely software cracks, unlicensed programs, and dubious internet tools. Specifically, it leverages single-use websites that offer trending items like new movies or software cracks. These sites often pushed to the top of search results through spam techniques, host malicious links that deliver ransomware.
Initially, cybercriminals inject downloader malware that paves the way for the ransomware by disabling security defenses, such as Windows Defender, and implementing changes to hinder antivirus programs from blocking or removing the ransomware.
The Qepi Virus Encryption Process
Upon entry, the Qepi ransomware disables common backup methods and blocks access to potential recovery solutions. It then systematically encrypts files, connecting to its server for an encryption key before starting the encryption process, which it repeats until all target files are encrypted.
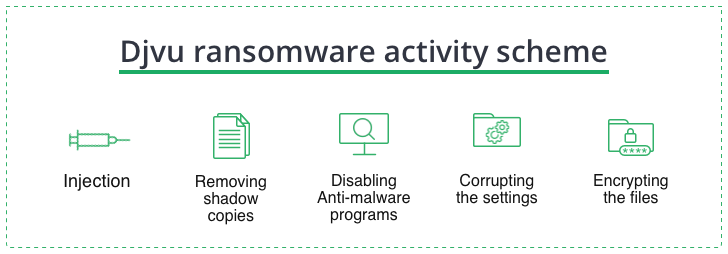
To ensure persistence, Qepi ransomware clones its executable file into obscure directories, avoiding detection by most antivirus software.
Removing Qepi and Ransomware Protection
Given its sophistication, detecting and removing ransomware demands the utmost care. The Qepi virus, known for hindering security software execution, requires you to bypass these restrictions for successful removal and system recovery.
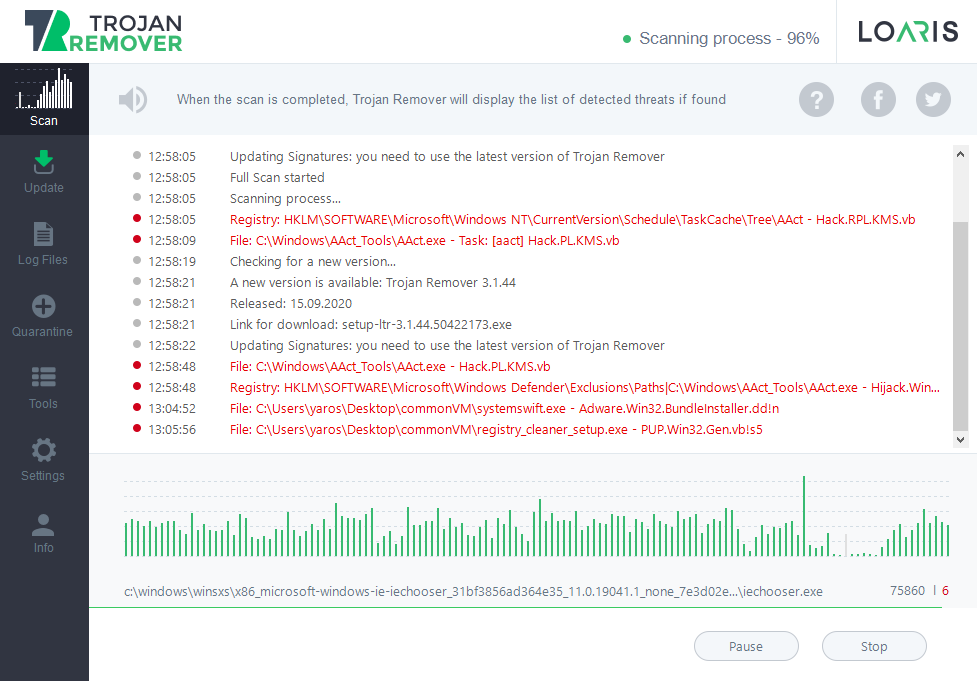
Loaris Trojan Remover stands out as the premier choice for eradicating the ransomware threat and restoring your system. It boasts an advanced scanning engine that detects ransomware in all forms and allows for targeted scans with its Custom Scan feature.
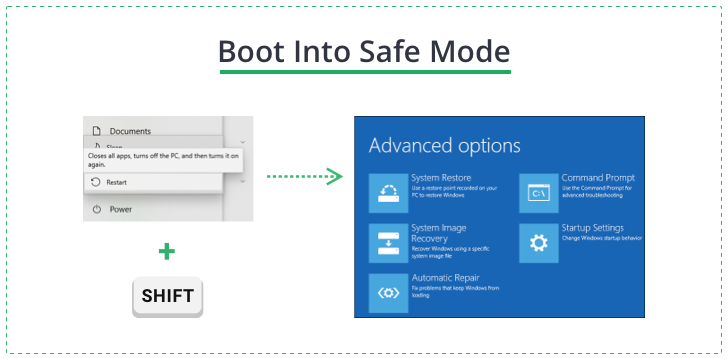
To navigate around the ransomware’s execution blocks, boot your PC in Safe Mode with Networking. This can be done through the Troubleshooting panel by restarting your PC while holding the Shift key, navigating to Startup Settings, and selecting Windows 10 Safe Mode with Networking.
In Safe Mode, launch the Loaris installer, follow the installation prompts, and activate the free trial for full functionality.
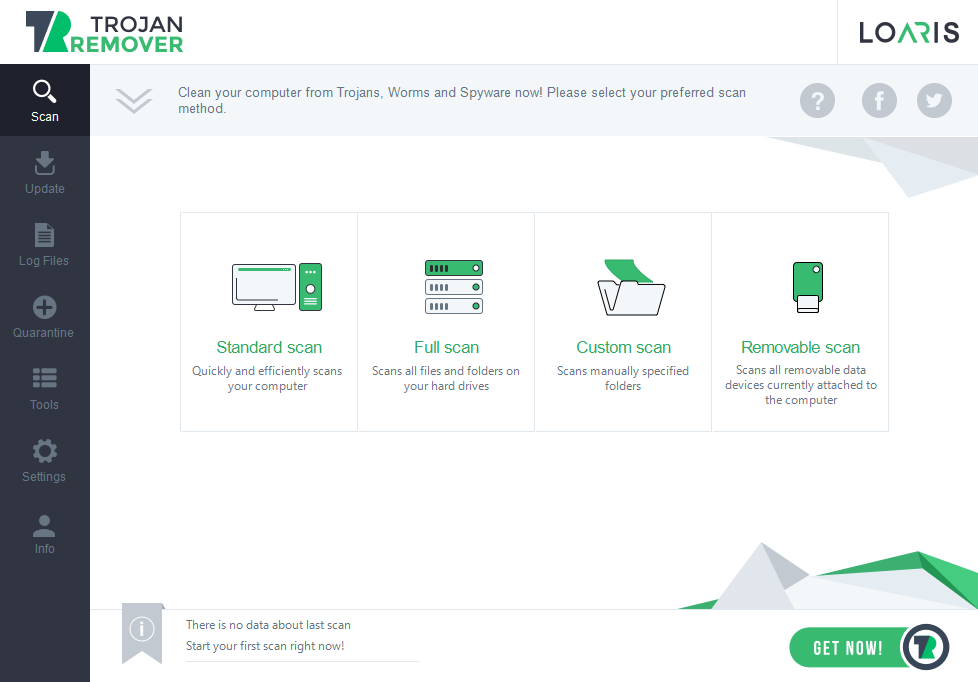
Conduct a full scan, review the list of detected threats, and proceed with the recommended removal actions.
Decrypting Qepi Files
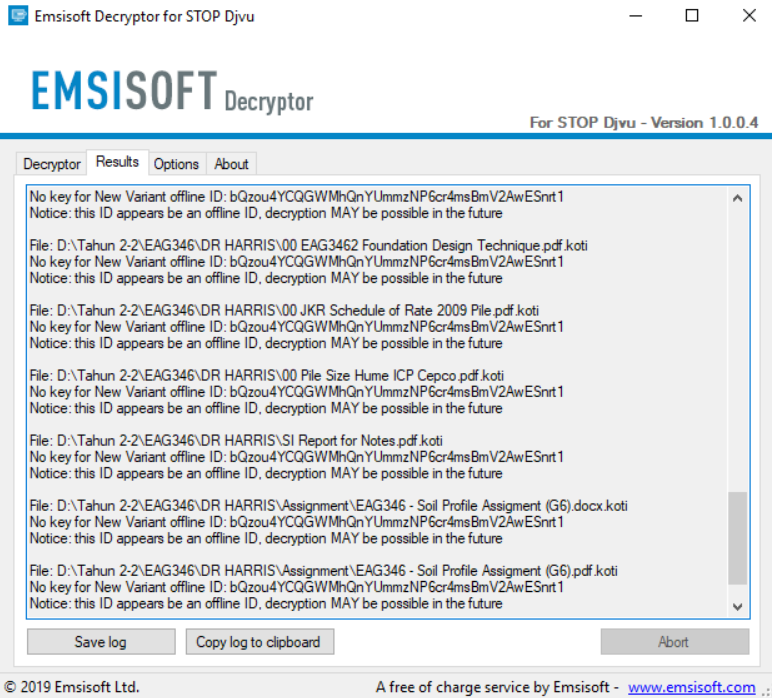
Decrypting files affected by Qepi ransomware might seem daunting, but not all hope is lost. The malware uses two key types – online and offline – with the latter offering a ray of hope for decryption.
Emsisoft’s free tool for STOP/Djvu decryption leverages collected keys to offer victims a chance at recovering their files.
Decryption with Emsisoft Decryptor for STOP Djvu
Install the Emsisoft Decryptor for STOP Djvu from the official website, set it up by specifying target folders, and initiate the decryption process.
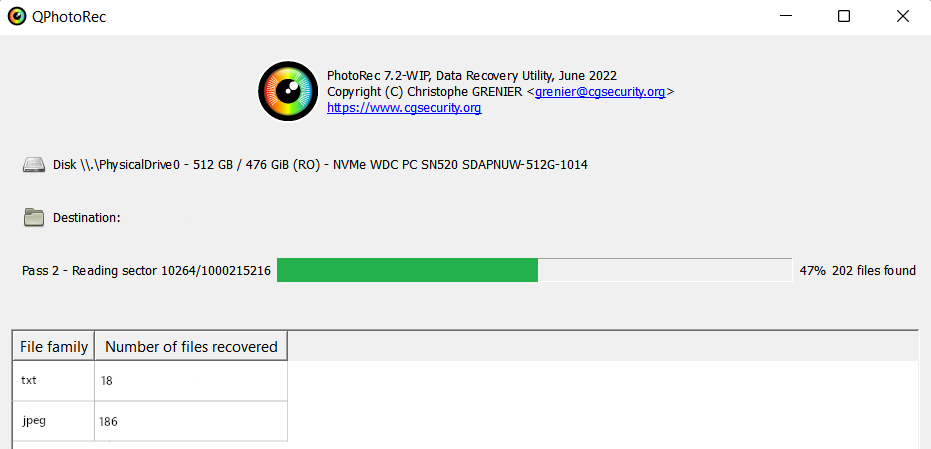
If Emsisoft’s tool cannot decrypt your files, consider file recovery tools as an alternative. For example, PhotoRec, a free tool, can recover files deleted by ransomware by searching for residual data left on the disk.
Recovering .Qepi Files with PhotoRec
Download PhotoRec, specify the disk or partition and desired file formats for recovery and start the recovery process to salvage your encrypted data.
Frequently Asked Questions
🤔 Can I decrypt the online key ID by myself?
Deciphering the online ID used by Qepi ransomware is currently beyond the reach of modern computing, potentially taking millions of years due to its complexity. The most effective alternative is employing file recovery tools, as detailed above.
🤔 Can Trojan Remover decrypt files?
While Trojan Remover excels at eliminating Qepi ransomware and repairing the aftermath on your PC, it doesn’t decrypt files. For decryption attempts, please use the recommended tools.