Have you received a warning from Windows Defender during a routine scan, alerting you to the presence of a threat called Trojan:Script/Wacatac.B!ml or Trojan:Win32/Wacatac.B!ml? Does the message indicate that Windows Defender attempted to remove the threat but was unsuccessful, necessitating further action? If so, your computer has been infected with the Wacatac Trojan, which Windows Defender has been unable to eliminate automatically. This guide will delve deeper into this Trojan, how it infiltrates your system, and what steps you should take to address it.
What Is Trojan:Script/Wacatac.B!ml?
Windows Defender classifies Wacatac.B!ml as a Trojan because it gains access to Windows operating systems by deceiving users into executing seemingly legitimate files.
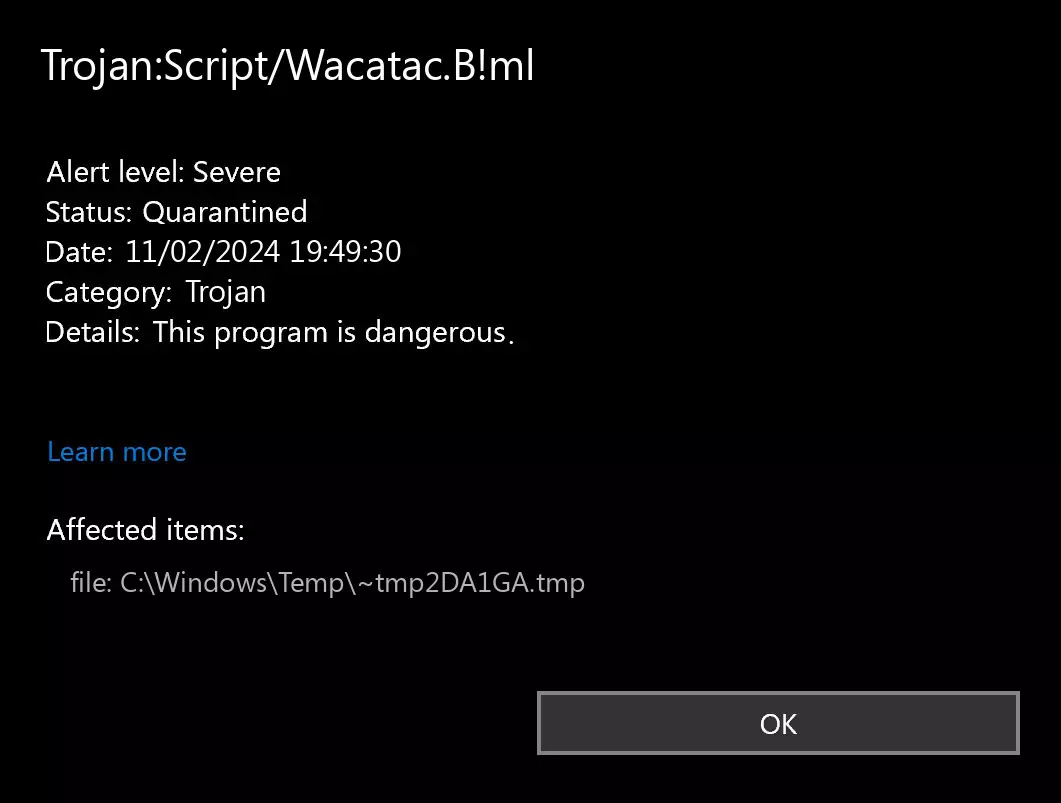
Once it infects your system, it exposes you to risks such as identity theft, data corruption, and financial harm. Moreover, it operates in the background, consuming resources unbeknownst to you, resulting in sluggish system performance.
| Detection | Trojan:Script/Wacatac.B!ml, Trojan:Win32/Wacatac.B!ml |
| Type | Windows Virus, Trojan |
| Device | Windows |
| Symptoms | No symptoms |
| Damage | Installing other malware, keystroke monitoring, personal data theft, your device added to a botnet |
Given these dangers, prompt removal is imperative. Even Microsoft Defender emphasizes the severity of this threat in its warning and urges immediate action. This begs the question: how did it breach your computer’s defenses?
How Did the Wacatac.B!ml Trojan Penetrate Your PC?
To understand the infiltration of the Wacatac Trojan, consider the following:
- Have you downloaded cracked versions of software or utilized Cracks to activate premium software for free?
- Have you obtained outdated software from suspicious websites?
- Recently, have you received seemingly genuine emails (such as shipment invoices) with attachments that, upon clicking, executed a script and disappeared?
- Did you acquire movies or music through torrent files to avoid purchasing them?
- Have you disabled Windows Defender or your antivirus for a period, only to find this threat upon re-scanning your computer? If you answered affirmatively to any of these questions, you’ve likely identified the entry point of the Wacatac Trojan. However, could it be a false positive? While plausible, it’s essential to first rule out this possibility.
Is Trojan:Script/Wacatac.B!ml a False Positive?
If your security scan has flagged a potential Trojan, confirming whether the Wacatac Trojan alert is indeed accurate or a false positive is important. Follow these steps:
- Go to the Online Virus Scanner.
- Locate the affected item where Windows Defender detected the Trojan.
- Select the suspicious file and upload it for analysis.
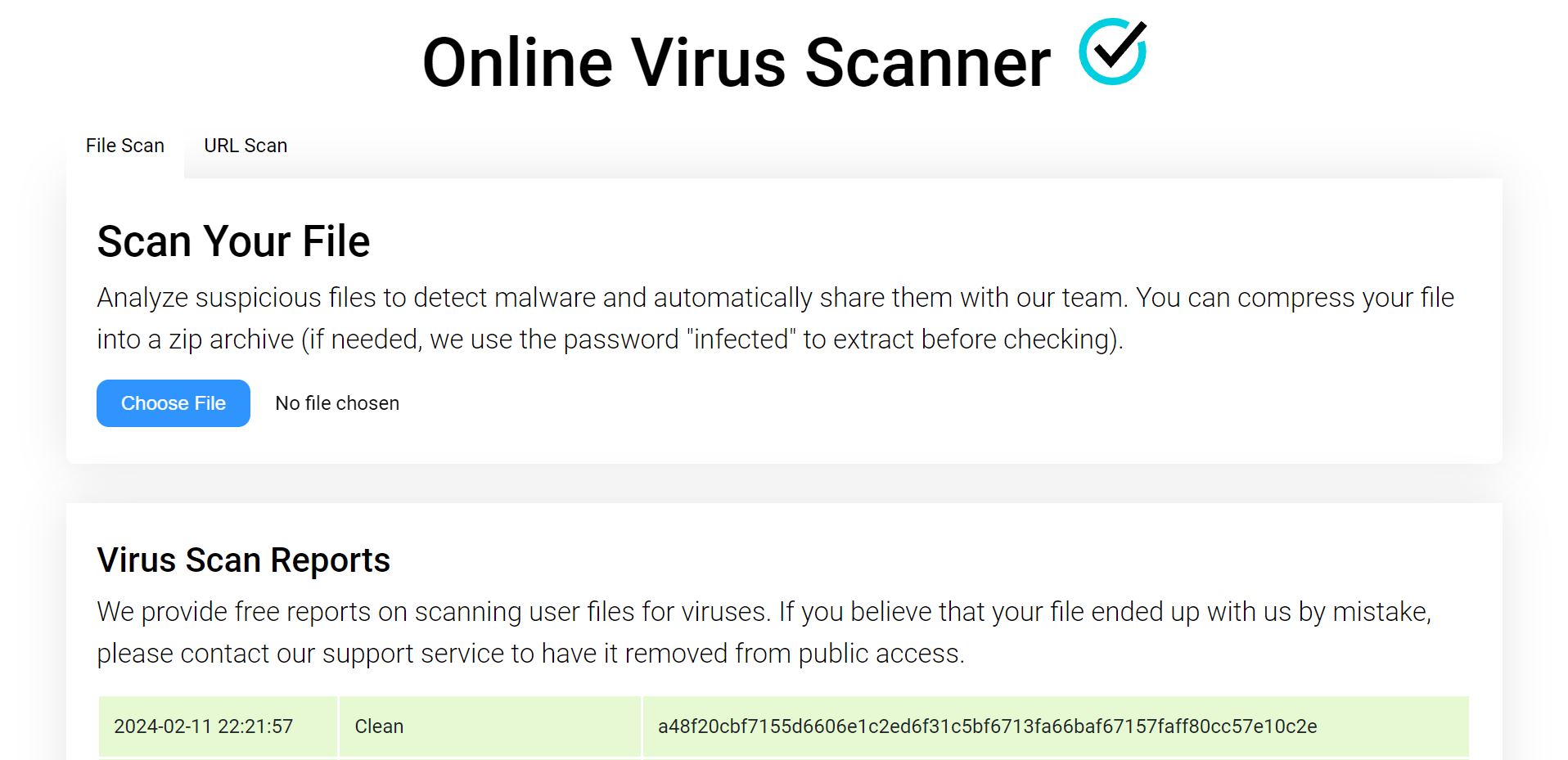
If the scan result comes back clean, it’s likely a false alarm. However, whether the file is clean or infected, it’s advisable to proceed with scanning and removal.
How to Remove Trojan:Script/Wacatac.B!ml
If the scan confirms the file’s infection, follow these steps:
Delete the Infected File
- The first step is to delete the infected file that Windows Defender claims is infected. Thus, navigate to the same path mentioned above, right-click on the file, and select Delete.
- After deleting the file, re-run a security check on your device. If the Trojan persists, proceed with the next solution.
Manual Removal of the Threat
Windows Security provides a straightforward method for manual threat removal. Here’s how:
- Press Win + I to open the Settings app.
- In the left sidebar, select Privacy & Security.
- Click on Windows Security in the right pane.
- Go to Virus & Threat Protection.
- Access Protection History.
- Locate the Wacatac threat and choose Remove from the Actions menu.
- If the threat persists, opt for Quarantine to contain it. Proceed to the next step.
Running a Malware Scan in Safe Mode
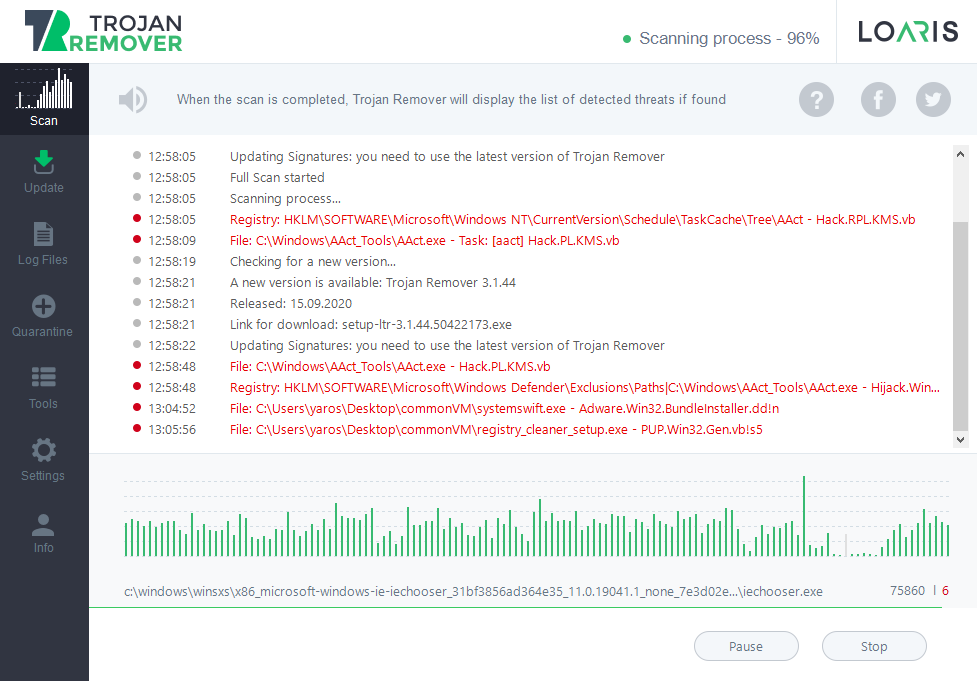
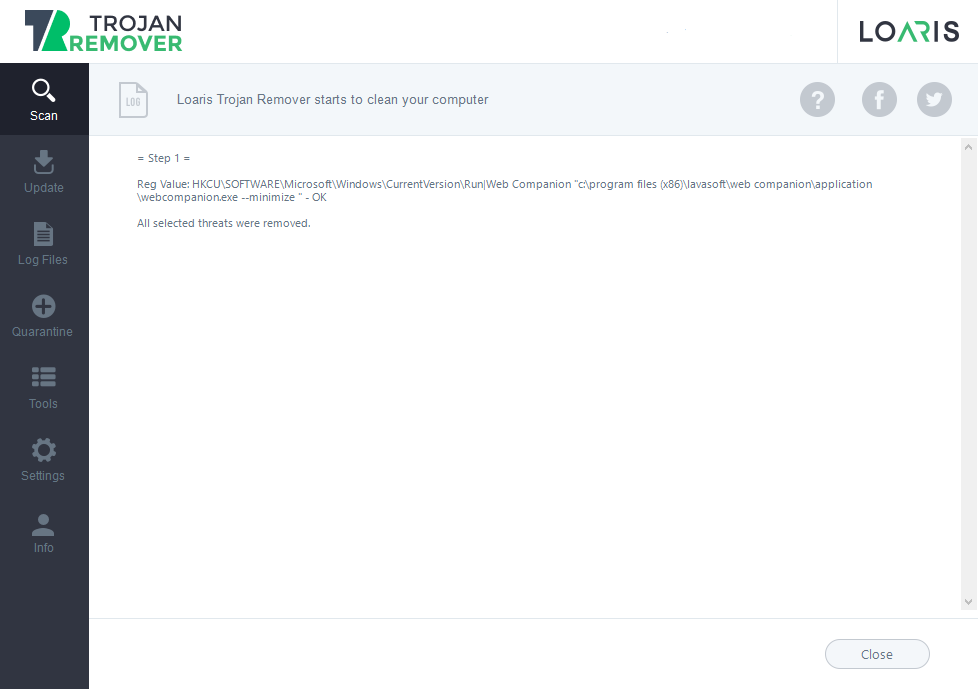
The best malware-removing software for this purpose is Loaris Trojan Remover. This application can remove the ransomware threat from your PC and repair the system after the attack. It has an advanced scanning mechanism that consists of three different modules that can detect trojans in any form. Additionally, you will be able to check up on all suspicious places with the Custom Scan function – it will scan the designated directory in just a minute.
It is important to mention that circumventing the ransomware that blocks the executive files launch requires booting into Safe Mode with Networking. You can download the installer before booting or after it – that will not matter at all.
To boot your PC into the Safe Mode, you must open the Troubleshooting panel. Press Win→Power, and then click on the Restart button while holding the Shift key. After that, you will see the Troubleshooting screen. Go to Startup Settings → Windows 10 Safe Mode with Networking. Press Enter and wait till your system is loading.
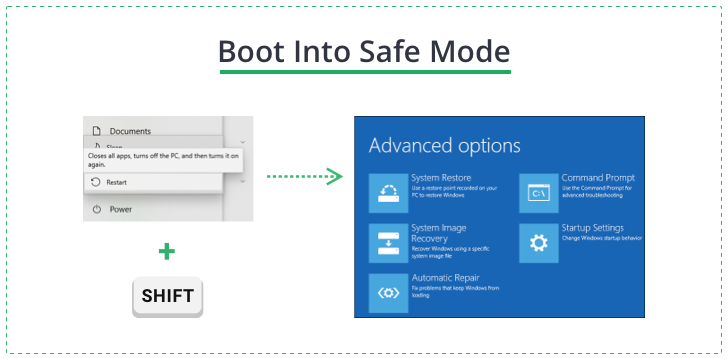
Safe Mode in Windows supposes the system loading without certain modules, in particular – the startup programs and a part of Group Policies. This mode is convenient for malware removal since it prevents the launch of programs not listed as systems and nails the majority of restrictions implemented by malware.
Remove Wacatac from Windows
When your PC is booted into Safe Mode, launch the Loaris installation file and wait until the program is installed. It may take several minutes. After that, the program will offer you to activate a free trial. This action is recommended since it allows you to use the full functionality of the Trojan Remover. Just enter your email address and receive a free trial code.
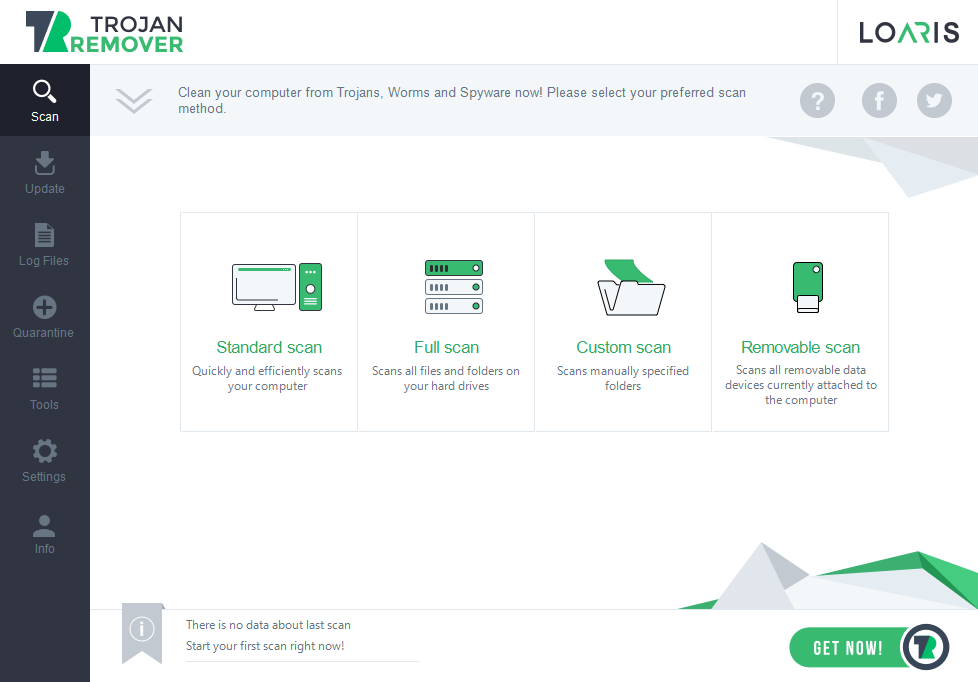
When the trial is activated, launch the full scan. It may last for 20-30 minutes, so keep patience. You can use your computer during this operation without any restrictions.
After the scan, you will see the list of detected threats. By default, the program designates suitable actions for each detection. In particular, for the Wacatac is a removed. However, you can manage these actions by clicking on the label on the right side of the detection if you think some detected items may need a different action.