Trojan:Win32/Casdet!rfn represents a significant threat to computer users, possessing the capability to conduct a range of malicious activities once it infiltrates a system. Its primary objectives include the theft of personal data, installation of further malware, and facilitating unauthorized access to compromised systems for remote attackers. Immediate measures are necessary to eradicate this malware from affected computers to protect data and system integrity.
Trojan:Win32/Casdet!rfn in Action
The insidious nature of Trojan:Win32/Casdet!rfn often means its presence goes unnoticed without clear, visible symptoms. However, subtle changes in system behavior or performance may indicate its activity. Among the actions it can undertake are:
- Personal Information Theft: Casdet!rfn is designed to harvest sensitive information, including login credentials, financial data, and personal identification, posing a severe privacy and security risk.
- Additional Malware Installation: The Trojan serves as a gateway for further infections, downloading and installing a variety of malicious software that can further damage or compromise the system.
- Remote Access Facilitation: By creating backdoors, Casdet!rfn allows attackers remote system access, leading to unauthorized control, data exfiltration, and additional exploitation.
Technical Insights into Trojan:Win32/Casdet!rfn
Trojan:Win32/Casdet!rfn employs sophisticated techniques to evade detection and analysis. These include:
| Executable Code Extraction | Utilization of binary packers to protect the malware from reverse engineering. |
| Process Injection Techniques | Including inter-process and process hollowing methods. |
| Creation of RWX Memory | Including peculiar HTTP traffic and multiple unique user agents, indicating potential malware communications. |
| Suspicious Network Activity | Including peculiar HTTP traffic and multiple unique user agents, indicating potential malware communications. |
| Encrypted or Compressed Data | To hide the malware code from antivirus solutions. |
| Anti-Forensics Measures | Including checks for debugging and forensic tools to avoid analysis. |
Distribution Methods of Trojan:Win32/Casdet!rfn
The dissemination of Trojan:Win32/Casdet!rfn is varied, utilizing methods such as:
- Email Spam: Leveraging deceptive emails that mimic legitimate notifications from known entities like DHL or Amazon.
- Malicious Advertisements: Exploiting web ads to spread malware, highlighting the risk of engaging with suspicious online advertisements.
- Unlicensed Software: The use of cracked or pirated software often carries hidden malware payloads, including Trojans like Casdet!rfn.
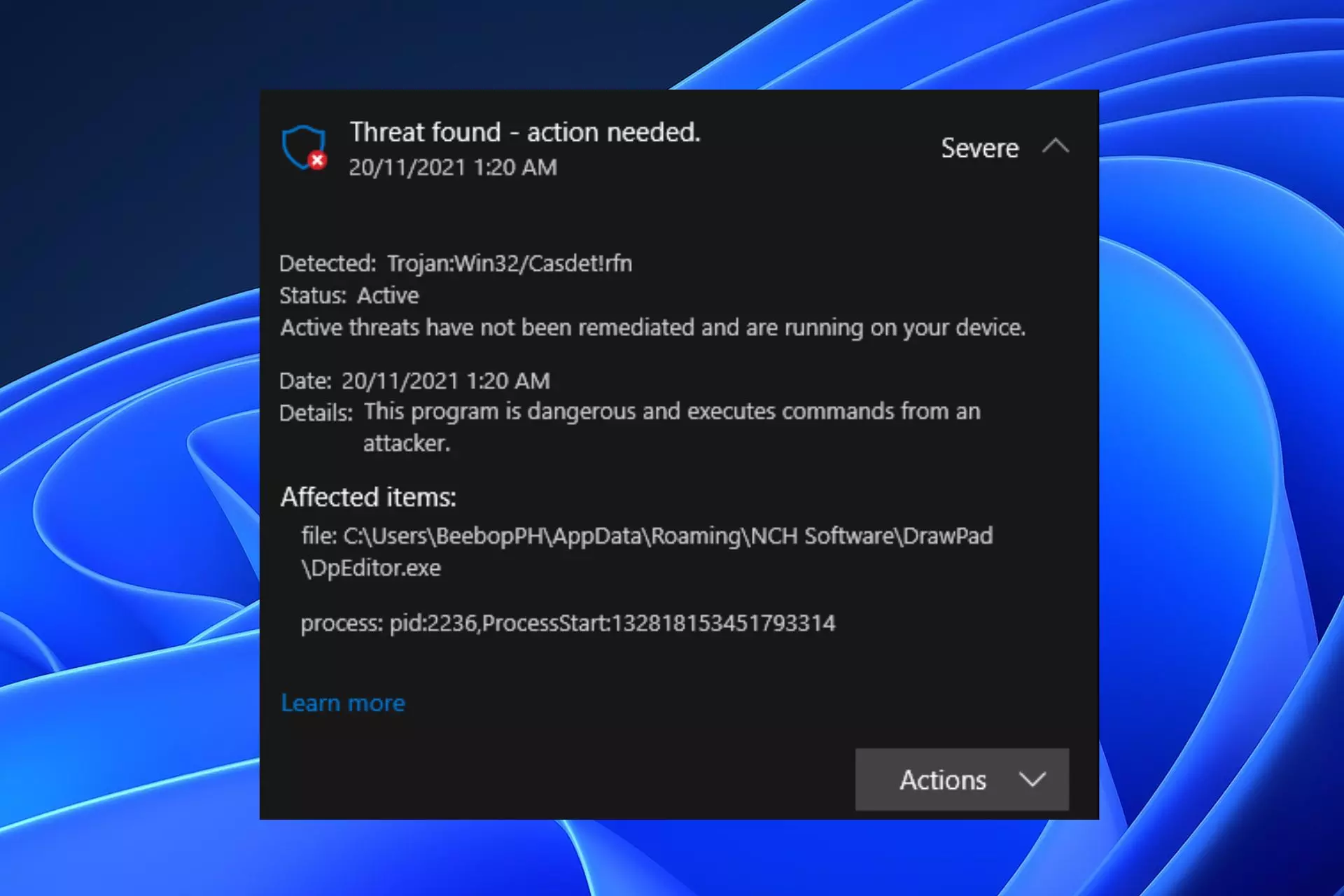
Detecting Trojan:Win32/Casdet!rfn
The infection signs can vary widely, but key indicators include:
- Disabled Windows Defender: A common target for malware to prevent detection and removal.
- Altered System Security Settings: Modifications to prevent the execution of security measures against malware.
- Password Theft: Risk of losing credentials stored on the system through decryption by the Trojan.
The stealth and complexity of Trojan:Win32/Casdet!rfn necessitate vigilant security practices, including the use of robust antivirus software, skepticism towards unsolicited emails, and avoidance of unlicensed software to mitigate the risk of infection. Immediate action to remove the Trojan upon detection is critical to safeguard personal and system security.
How to remove Trojan:Win32/Casdet!rfn?
Loaris Trojan Remover stands out as the premier choice for eradicating the ransomware threat and restoring your system. It boasts an advanced scanning engine that detects ransomware in all forms and allows for targeted scans with its Custom Scan feature.
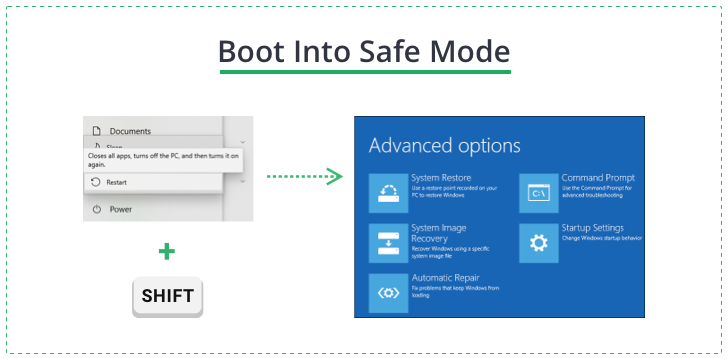
To navigate around the ransomware’s execution blocks, boot your PC in Safe Mode with Networking. This can be done through the Troubleshooting panel by restarting your PC while holding the Shift key, navigating to Startup Settings, and selecting Windows 10 Safe Mode with Networking.
In Safe Mode, launch the Loaris installer, follow the installation prompts, and activate the free trial for full functionality.
When your PC is booted into Safe Mode, launch the Loaris installation file and wait until the program is installed. It may take several minutes. After that, the program will offer you to activate a free trial. This action is recommended since it allows you to use the full functionality of the Trojan Remover. Just enter your email address and receive a free trial code.
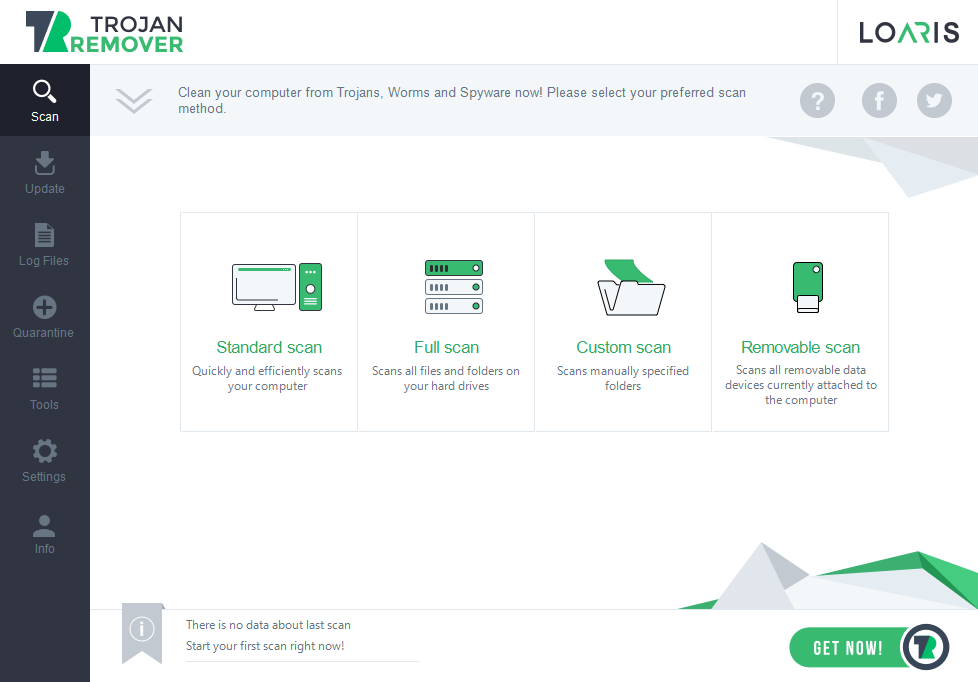
When the trial is activated, launch the full scan. It may last for 20-30 minutes, so keep patience. You can use your computer during this operation without any restrictions.
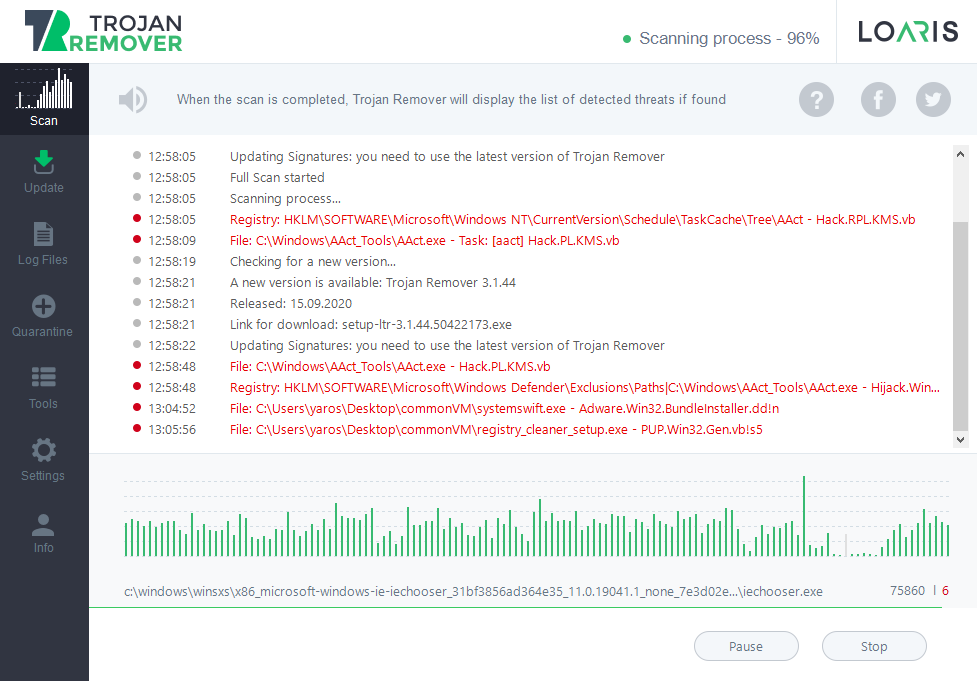
After the scan, you will see the list of detected threats. By default, the program designates suitable actions for each detection. In particular, for the Trojan:Win32/Casdet!rfn is a removed. However, you can manage these actions by clicking on the label on the right side of the detection if you think some detected items may need a different action.
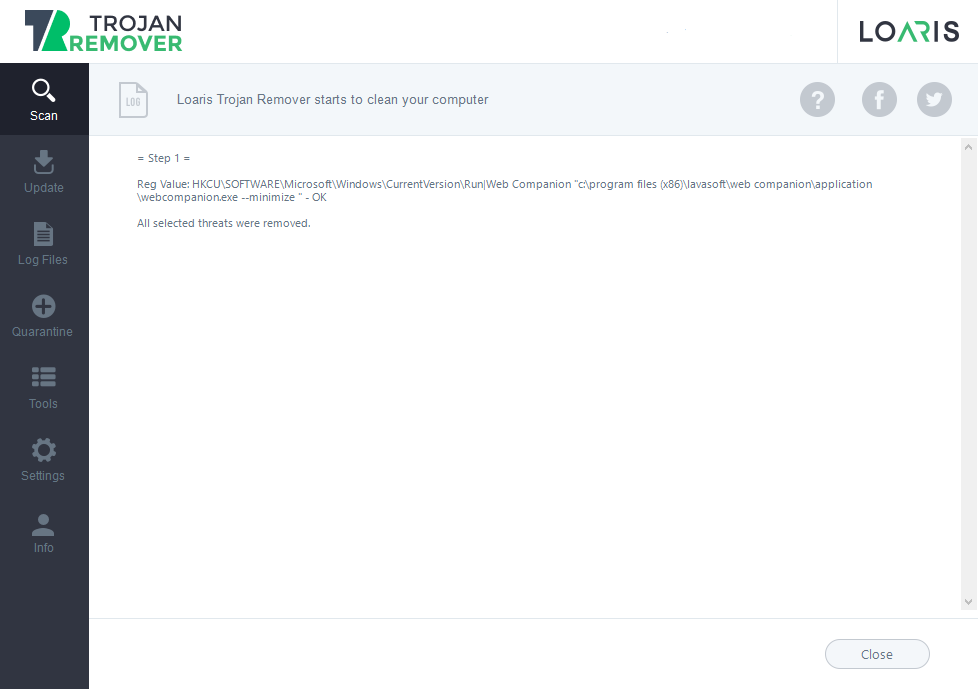
Conversely, if the Trojan Remover identifies malware, reboot your PC to halt any malware processes active in Windows memory. Conducting another full system scan post-restart is prudent to catch any potentially replicated malware. This subsequent scan will be quicker, focusing on recently added or modified files.
Complete the second scan and move to the next steps if it detects no malware. If it identifies malware, revisit your quarantine list, eliminate any verified threats, and then restart your PC. Repeat these steps until your system is clear of malware.