木馬:O97M/馬德巴!普茲 是一種惡意軟體, 俗稱木馬, 以 Microsoft Office 文件為目標. 具體來說, 它會影響使用舊版的 Microsoft Office 所建立的文件, 例如辦公室 97-2003 (.文件, ..xls, .PPT文件).
像 Madeba 這樣的木馬!pz 通常會利用 Office 套件中的漏洞在開啟受感染的文件時執行惡意程式碼. 一旦激活, 他們可能會做出各種有害的行為, 例如竊取敏感資訊, 損害系統安全, 或在受感染的電腦上安裝其他惡意軟體.
木馬:Win32/卡德特!rfn 的實際應用

木馬:O97M/馬德巴!pz可以透過多種方法注入Windows PC, 主要利用軟體中的漏洞或透過社會工程策略. 以下是對其感染系統的潛在方式的分析:
- 電子郵件附件: 常見的方法是透過惡意電子郵件附件. 攻擊者可能會假裝來自合法來源發送電子郵件, 例如同事, 朋友, 或值得信賴的組織. 這些電子郵件通常包含看似無害的附件, 例如Word文檔, Excel 試算表, 或 PowerPoint 簡報. 然而, 這些檔案包含惡意巨集或腳本, 執行時, 在您的系統上下載並執行木馬.
- 路過式下載: 另一種方法涉及路過式下載, 當您造訪受感染或惡意網站時,特洛伊木馬會以靜默方式下載並安裝在您的系統上. 這些網站利用您的瀏覽器或瀏覽器外掛程式中的漏洞在您不知情的情況下執行惡意程式碼.
- 受感染的外部設備: 木馬:O97M/馬德巴!pz 也可以透過受感染的外部裝置(例如 USB 隨身碟)傳播, 外接硬碟, 甚至智慧型手機. 當您將受感染的裝置連接到您的電腦時, 該木馬可能會自動執行並感染您的系統.
- 利用軟體漏洞: 木馬:O97M/馬德巴!pz 經常利用軟體應用程式中的漏洞來未經授權地存取您的系統. 這可能包括 Microsoft Office 中的漏洞, 網路瀏覽器, 或其他常用軟體. 攻擊者透過製作專門設計的文件或文件來利用這些漏洞, 打開時, 觸發惡意程式碼的執行.
- 社會工程學: 攻擊者可能會使用社會工程策略來誘騙您手動下載並執行木馬. 例如, 他們可能會創建虛假網站或廣告,聲稱提供免費軟體, 遊戲, 或媒體內容. 當您下載並運行這些文件時, 您無意中在系統上安裝了木馬.
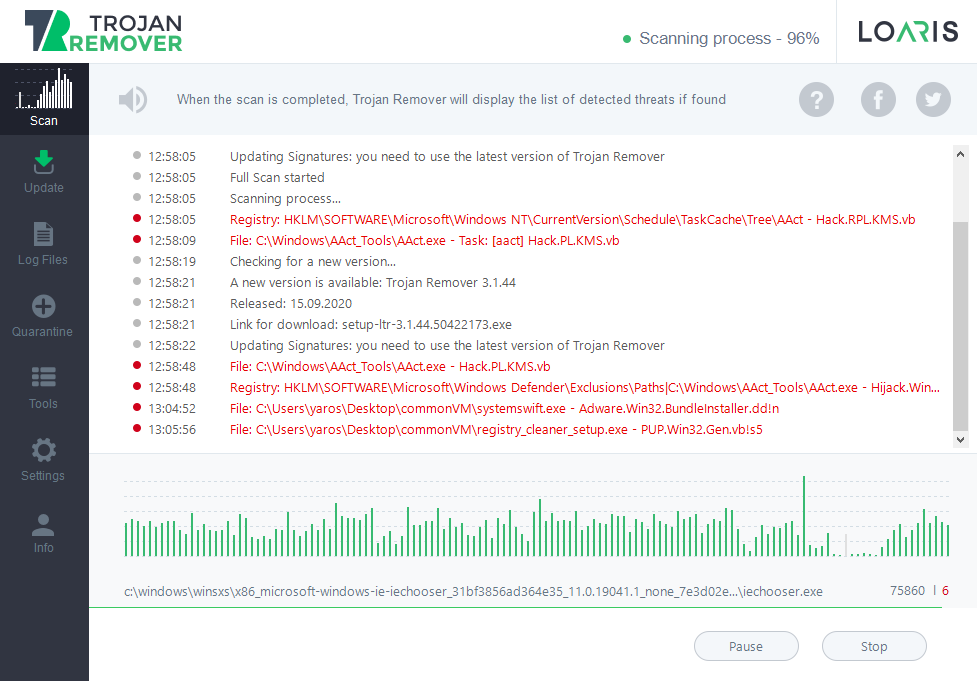
木馬:O97M/馬德巴!pz 透過前面提到的方法之一傳遞到受害者的系統, 例如電子郵件附件, 路過式下載, 受感染的外部設備, 或利用軟體漏洞.
一旦惡意檔案被開啟或執行, 木馬代碼被激活. 這可能涉及利用軟體應用程式中的漏洞, 在 Microsoft Office 文件中執行惡意宏, 或利用其他方式來執行其有效負載.
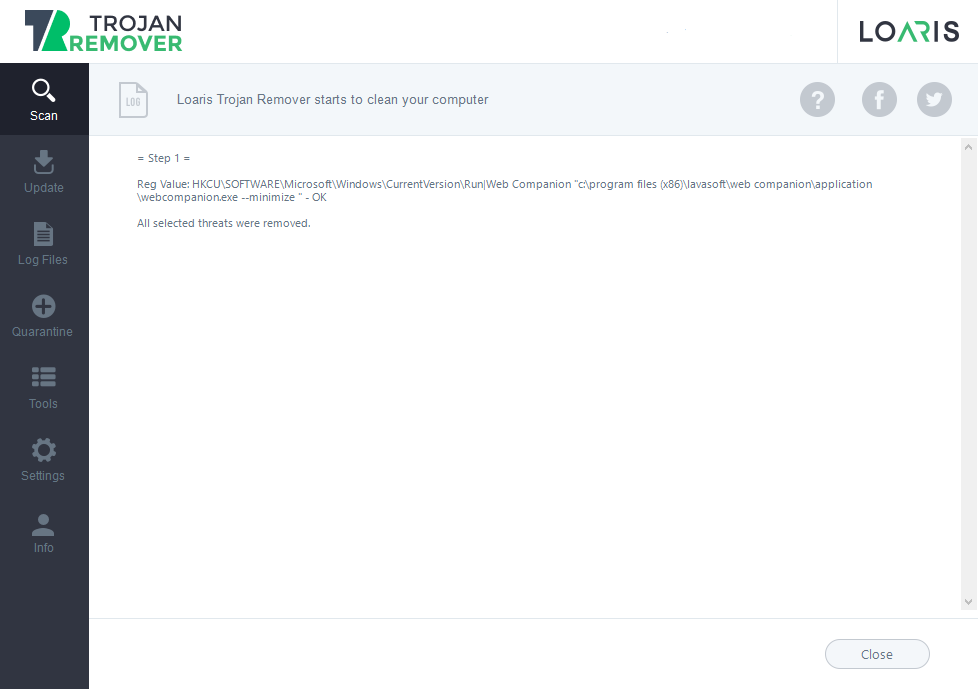
特洛伊木馬 Madeba 在受感染的系統上持續存在,以確保即使在系統重新啟動後它仍保持活動狀態. 它可以透過建立註冊表項來實現這一點, 修改系統檔案, 或將其安裝為服務或啟動程序.
建立堅持後, 木馬執行其有效負載. 此有效負載可能包含各種惡意活動, 例如竊取敏感資訊, 記錄擊鍵, 擷取螢幕截圖, 加密文件以勒索贖金, 或將受感染的系統變成機器人以在殭屍網路中使用.
它可能會嘗試與遠端命令和控制進行通信 (C&C) 攻擊者操作的伺服器. 這種通訊允許攻擊者向受感染的系統發送命令, 找回被盜數據, 或使用新指令或有效負載更新木馬.
木馬:O97M/馬德巴!pz 採用規避技術來避免被防毒或安全軟體偵測. 這可能包括每次感染時都會改變其外觀的多態代碼, 混淆技術以隱藏其真實目的, 或反分析措施來阻止逆向工程嘗試.
木馬:O97M/馬德巴!pz 可以傳播到網路上或透過可移動驅動器的其他系統. 他們試圖利用網路服務中的漏洞或使用社會工程策略來誘騙同一網路上的使用者執行惡意軟體. 它刪除日誌, 修改系統檔案, 或以其他方式試圖隱藏其在受感染系統上的存在.
木馬:O97M/馬德巴!總結
木馬:Win32/卡德特!rfn 採用複雜的技術來逃避偵測與分析. 這些包括: