Truva atı:O97M/Madeba!pz bir tür kötü amaçlı yazılımdır, genellikle Truva atı olarak bilinir, Microsoft Office belgelerini hedefleyen. özellikle, Microsoft Office'in eski sürümleriyle oluşturulan dosyaları etkiler, Ofis gibi 97-2003 (.doktor, .xls, .ppt dosyaları).
Madeba gibi Truva atları!pz genellikle, virüslü belge açıldığında kötü amaçlı kod yürütmek için Office paketindeki güvenlik açıklarından yararlanarak çalışır.. Etkinleştirildikten sonra, çeşitli zararlı eylemler gerçekleştirebilirler, hassas bilgilerin çalınması gibi, sistem güvenliğinden ödün verilmesi, veya virüslü bilgisayara ek kötü amaçlı yazılım yükleme.
Truva atı:Win32/Kaset!rfn Eylemde

Truva atı:O97M/Madeba!pz çeşitli yöntemlerle Windows PC'ye enjekte edilebilir, öncelikle yazılımdaki güvenlik açıklarından veya sosyal mühendislik taktiklerinden yararlanmak. İşte sisteminize bulaşabileceği potansiyel yolların bir analizi:
- Email ekleri: Yaygın yöntemlerden biri, kötü amaçlı e-posta ekleridir. Saldırganlar meşru kaynaklardan geliyormuş gibi görünen e-postalar gönderebilir, bir meslektaşım gibi, arkadaş, veya güvenilir kuruluş. Bu e-postalar genellikle zararsız görünen ekler içerir, Word belgeleri gibi, Excel elektronik tabloları, veya PowerPoint sunumları. Fakat, bu dosyalar kötü amaçlı makrolar veya komut dosyaları içerir., yürütüldüğünde, Trojan'ı sisteminize indirin ve çalıştırın.
- Drive-By İndirmeleri: Başka bir yöntem, arabadan indirmeleri içerir, Güvenliği ihlal edilmiş veya kötü amaçlı bir web sitesini ziyaret ettiğinizde Truva atının sisteminize sessizce indirilip yüklendiği yer. Bu web siteleri, bilginiz olmadan kötü amaçlı kod yürütmek için tarayıcınızdaki veya tarayıcı eklentilerinizdeki güvenlik açıklarından yararlanır..
- Virüslü Harici Cihazlar: Truva atı:O97M/Madeba!pz ayrıca USB sürücüler gibi virüslü harici cihazlara da yayılabilir, harici sabit diskler, ve hatta akıllı telefonlar. Virüs bulaşmış bir cihazı bilgisayarınıza bağladığınızda, Trojan otomatik olarak çalıştırılıp sisteminize bulaşabilir.
- Yazılımdaki Açıklardan Yararlanma: Truva atı:O97M/Madeba!pz, sisteminize yetkisiz erişim sağlamak için sıklıkla yazılım uygulamalarındaki güvenlik açıklarından yararlanır. Bu, Microsoft Office'teki güvenlik açıklarını içerebilir, internet tarayıcıları, veya yaygın olarak kullanılan diğer yazılımlar. Saldırganlar, özel olarak tasarlanmış belgeler veya dosyalar hazırlayarak bu güvenlik açıklarından yararlanır., açıldığında, kötü amaçlı kodun yürütülmesini tetiklemek.
- Sosyal mühendislik: Saldırganlar, Truva atını manuel olarak indirmeniz ve çalıştırmanız için sizi kandırmak amacıyla sosyal mühendislik taktiklerini kullanabilir.. Örneğin, ücretsiz yazılım sunduğunu iddia eden sahte web siteleri veya reklamlar oluşturabilirler, oyunlar, veya medya içeriği. Bu dosyaları indirip çalıştırdığınızda, Trojan'ı yanlışlıkla sisteminize yüklediğinizde.
Truva atı:O97M/Madeba!pz, daha önce bahsedilen yöntemlerden biri aracılığıyla kurbanın sistemine iletilir, e-posta ekleri gibi, arabayla indirilenler, virüslü harici cihazlar, veya yazılım açıklarından faydalanmak.
Kötü amaçlı dosya açıldığında veya yürütüldüğünde, Truva atının kodu etkinleştirildi. Bu, yazılım uygulamalarındaki güvenlik açıklarından yararlanmayı içerebilir, Microsoft Office belgelerinde kötü amaçlı makrolar çalıştırma, veya yükünü yürütmek için başka yöntemlerden yararlanmak.
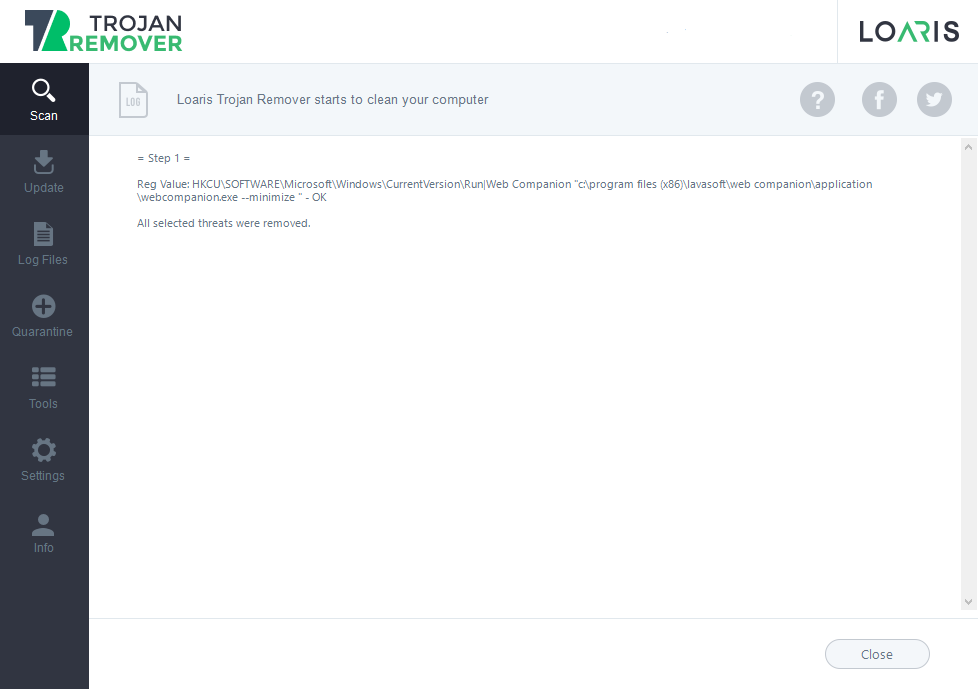
Sistem yeniden başlatıldıktan sonra bile aktif kalmasını sağlamak için virüslü sistemde Trojan Madeba'nın kalıcılığı. Bunu kayıt defteri girişleri oluşturarak başarabilir, sistem dosyalarını değiştirme, veya kendisini bir hizmet veya başlangıç programı olarak yükleme.
Kalıcılığı sağladıktan sonra, Truva atı yükünü yürütür. Bu veri çeşitli kötü amaçlı etkinlikleri içerebilir, hassas bilgilerin çalınması gibi, tuş vuruşlarını günlüğe kaydetme, ekran görüntüleri yakalama, fidye için dosyaları şifrelemek, veya virüs bulaşmış sistemi bir botnet'te kullanılmak üzere bir bot'a dönüştürmek.
Uzaktan komuta ve kontrol ile iletişim kurmaya çalışabilir (C&C) saldırganlar tarafından işletilen sunucular. Bu iletişim, saldırganların virüslü sisteme komut göndermesine olanak tanır, çalınan verileri geri al, veya Truva atını yeni talimatlar veya yüklerle güncelleyin.
Truva atı:O97M/Madeba!pz, antivirüs veya güvenlik yazılımı tarafından tespit edilmekten kaçınmak için kaçırma teknikleri kullanır. Bu, her enfeksiyonda görünümünü değiştiren polimorfik kodu içerebilir., gerçek amacını gizlemek için şaşırtma teknikleri, veya tersine mühendislik girişimlerini engellemek için anti-analiz önlemleri.
Truva atı:O97M/Madeba!pz, ağdaki diğer sistemlere veya çıkarılabilir sürücüler aracılığıyla yayılabilir. Ağ hizmetlerindeki güvenlik açıklarından yararlanmaya veya aynı ağdaki kullanıcıları kötü amaçlı yazılımı çalıştırmaları için kandırmak için sosyal mühendislik taktiklerini kullanmaya çalışıyorlar. Günlükleri siler, sistem dosyalarını değiştirir, veya başka bir şekilde virüslü sistemdeki varlığını gizlemeye çalışır.
Truva atı:O97M/Madeba!Özet
Truva atı:Win32/Kaset!rfn, tespit ve analizden kaçınmak için gelişmiş teknikler kullanır. Bunlar şunları içerir::