troiano:O97M/Madeba!pz é um tipo de software malicioso, comumente conhecido como Trojan, direcionado a documentos do Microsoft Office. Especificamente, afeta arquivos criados com versões mais antigas do Microsoft Office, como escritório 97-2003 (.documento, .xls, .arquivos ppt).
Trojans como Madeba!pz normalmente funciona explorando vulnerabilidades no pacote Office para executar código malicioso quando o documento infectado é aberto. Uma vez ativado, eles podem realizar várias ações prejudiciais, como roubar informações confidenciais, comprometendo a segurança do sistema, ou instalar malware adicional no computador infectado.
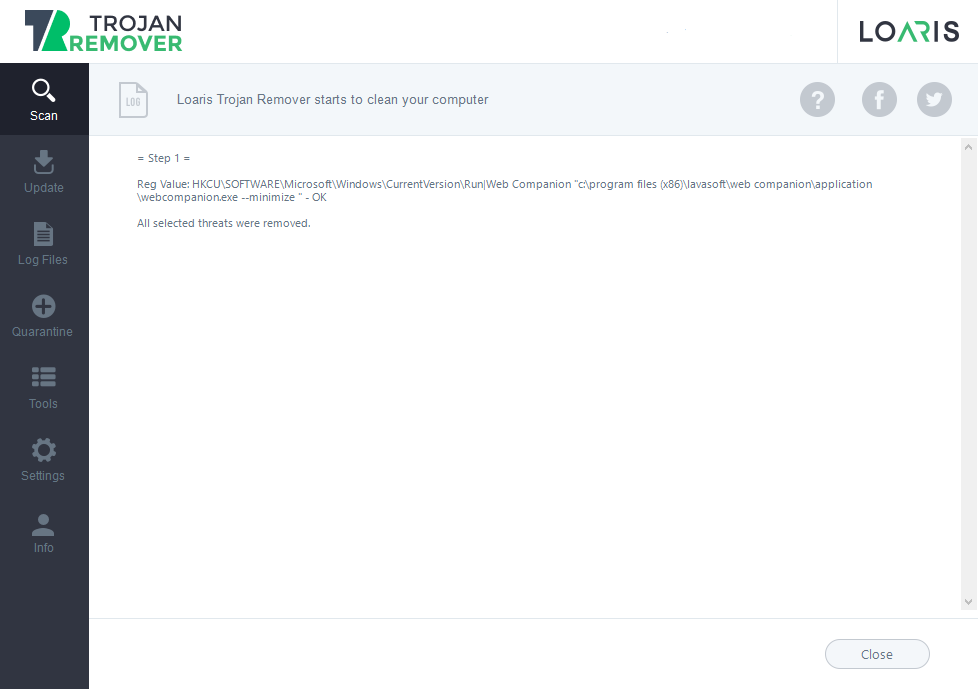
troiano:Win32/Casdet!rfn em ação

troiano:O97M/Madeba!pz pode ser injetado em um PC com Windows através de vários métodos, explorando principalmente vulnerabilidades em software ou por meio de táticas de engenharia social. Aqui está uma análise das possíveis maneiras pelas quais ele pode infectar seu sistema:
- Anexos de e-mail: Um método comum é através de anexos de e-mail maliciosos. Os invasores podem enviar e-mails fingindo ser de fontes legítimas, como um colega, amigo, ou organização confiável. Esses e-mails geralmente contêm anexos que parecem inofensivos, como documentos do Word, Planilhas Excel, ou apresentações em PowerPoint. No entanto, esses arquivos contêm macros ou scripts maliciosos que, quando executado, baixe e execute o Trojan em seu sistema.
- Downloads drive-by: Outro método envolve downloads drive-by, onde o Trojan é baixado e instalado silenciosamente em seu sistema quando você visita um site comprometido ou malicioso. Esses sites exploram vulnerabilidades no seu navegador ou plug-ins do navegador para executar códigos maliciosos sem o seu conhecimento.
- Dispositivos externos infectados: troiano:O97M/Madeba!pz também pode se espalhar através de dispositivos externos infectados, como unidades USB, discos rígidos externos, ou até smartphones. Quando você conecta um dispositivo infectado ao seu PC, o Trojan pode executar e infectar automaticamente o seu sistema.
- Explorando vulnerabilidades de software: troiano:O97M/Madeba!pz frequentemente explora vulnerabilidades em aplicativos de software para obter acesso não autorizado ao seu sistema. Isso pode incluir vulnerabilidades no Microsoft Office, navegadores da web, ou outro software comumente usado. Os invasores exploram essas vulnerabilidades criando documentos ou arquivos especialmente projetados que, quando aberto, desencadear a execução de código malicioso.
- Engenharia social: Os invasores podem usar táticas de engenharia social para induzi-lo a baixar e executar manualmente o Trojan. Por exemplo, eles podem criar sites falsos ou anúncios que afirmam oferecer software gratuito, jogos, ou conteúdo de mídia. Quando você baixa e executa esses arquivos, você inadvertidamente instala o Trojan em seu sistema.
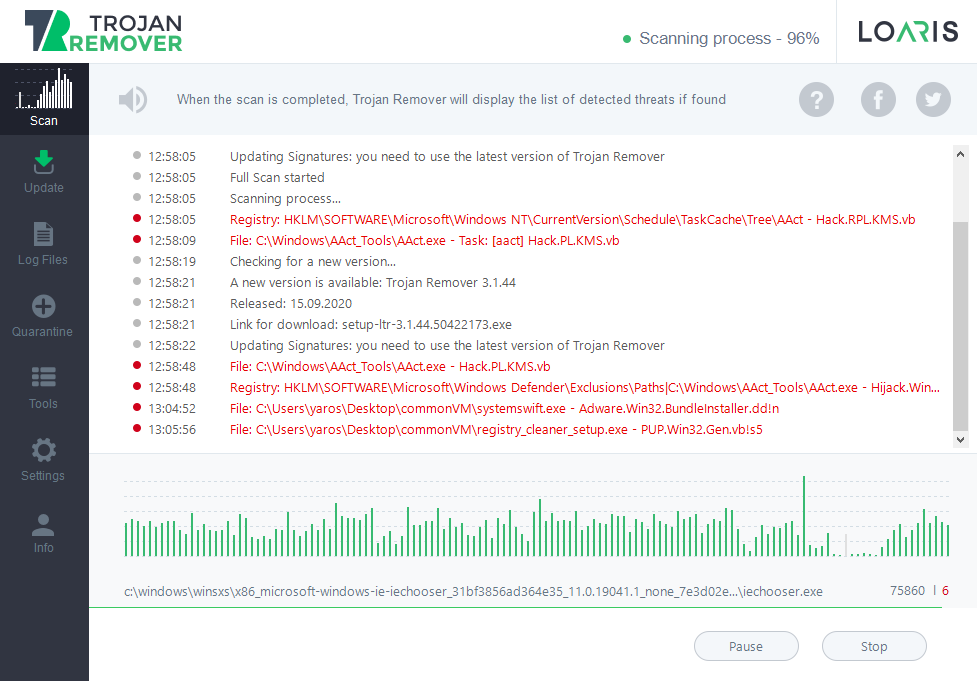
troiano:O97M/Madeba!pz é entregue ao sistema da vítima através de um dos métodos mencionados anteriormente, como anexos de e-mail, downloads drive-by, dispositivos externos infectados, ou explorar vulnerabilidades de software.
Depois que o arquivo malicioso for aberto ou executado, o código do Trojan está ativado. Isso pode envolver a exploração de vulnerabilidades em aplicativos de software, executando macros maliciosas em documentos do Microsoft Office, ou aproveitando outros meios para executar sua carga útil.
Persistência do Trojan Madeba no sistema infectado para garantir que ele permaneça ativo mesmo após a reinicialização do sistema. Isso pode ser conseguido criando entradas de registro, modificando arquivos do sistema, ou se instalando como um serviço ou programa de inicialização.
Depois de estabelecer persistência, o Trojan executa sua carga útil. Esta carga pode incluir várias atividades maliciosas, como roubar informações confidenciais, registrando pressionamentos de tecla, captura de tela, criptografando arquivos para resgate, ou transformar o sistema infectado em um bot para uso em uma botnet.
Ele pode tentar se comunicar com comando e controle remoto (C&C) servidores operados pelos invasores. Esta comunicação permite que os invasores enviem comandos ao sistema infectado, recuperar dados roubados, ou atualize o Trojan com novas instruções ou cargas úteis.
troiano:O97M/Madeba!pz emprega técnicas de evasão para evitar a detecção por antivírus ou software de segurança. Isso pode incluir código polimórfico que muda de aparência a cada infecção, técnicas de ofuscação para ocultar seu verdadeiro propósito, ou medidas anti-análise para impedir tentativas de engenharia reversa.
troiano:O97M/Madeba!pz pode se espalhar para outros sistemas na rede ou através de unidades removíveis. Eles tentam explorar vulnerabilidades em serviços de rede ou usam táticas de engenharia social para induzir os usuários na mesma rede a executar o malware.. Exclui registros, modifica arquivos do sistema, ou de outra forma tenta ocultar sua presença no sistema infectado.
troiano:O97M/Madeba!Resumo pz
troiano:Win32/Casdet!rfn emprega técnicas sofisticadas para evitar detecção e análise. Esses incluem: