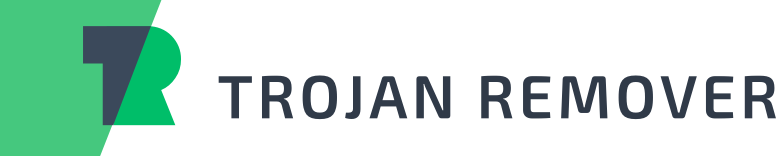
Cet article dévoile le nouveau cheval de Troie populaire, Win64:Génération de logiciels malveillants, mis en lumière par les systèmes antivirus Avast et Avg pour les fichiers suspects mais non classifiés. Contrairement à d'autres chevaux de Troie ou virus, Win64:Malware Gen partage certaines similitudes mais se distingue également de manière unique. Plongez pour plus de détails.
Avast continue d'attraper des virus: Win64:Génération de logiciels malveillants
j'ai ce problème, où Avast continue d'attraper ce virus appelé Win64:Des logiciels malveillants encore et encore pendant environ 20 jours maintenant, et je ne suis pas sûr de ce que je devrais faire à ce sujet. J'ai ajouté les journaux de Malwarebytes et de Farbar Recovery Scan Tool. Le fichier infecté est wmcodecs.dll et l'emplacement est C:WindowsSystème32. Je pense que le scanner d'arrière-plan Avast le détecte. Peut-être pourriez-vous m'aider à résoudre ce problème?Forum.avast.com
Qu'est-ce que Win64:Malware-gen in Avast?
Avast Antivirus a conçu et utilisé Win64:Malware-gen comme méthode de détection heuristique pour identifier les chevaux de Troie de manière générique. Ce malware, Win64 Malware gen exe, pourrait se manifester sous forme de ransomware, détourner et chiffrer des fichiers sur l'ordinateur infecté et exiger un paiement pour leur libération.
Typiquement, le Win64:Un ransomware de génération malveillante incite les victimes à transférer de l'argent, visant à atténuer les risques que le cheval de Troie fait peser sur l'appareil concerné.
Les impacts sur les ordinateurs ciblés incluent généralement:
- Ouverture, édition, modification, renommer, cryptage, en mouvement, distribuer, suppression, ou détruire des fichiers.
- Mener une activité réseau sans être détecté, comme Win64:Malware-gen dissimule son activité réseau malgré l'API de Microsoft dans le système d'exploitation Windows conçue pour révéler une telle activité au cours de la dernière 30 jours.
- Bloquer l'accès de routine au poste de travail infecté, une tactique courante des virus connue sous le nom de casiers, jusqu'à ce que l'utilisateur paie une rançon.
Comment Win64:Malware-gen infecte un ordinateur?
Win64 Malware-gen infiltre les machines principalement via Hameçonnage e-mails ou par les utilisateurs rencontrant des logiciels nuisibles en ligne. Des voies supplémentaires incluent les téléchargements à partir de sources douteuses, torrent sites Internet, liens étranges, fausses mises à jour, et autres voies peu sûres.
Comment fonctionne la génération de logiciels malveillants Win64?
En cas d'infection, Win64:Malware-gen crypte les données ou perturbe les programmes’ Fonctionnalité. Il génère ensuite une demande de rançon exigeant le paiement du décryptage des données ou du déblocage de l'application., généralement révélé au redémarrage après un détournement.
La propagation de Win64 Malware-Gen est mondiale, adapter ses demandes de rançon et ses notifications aux nuances locales ou régionales.
Par exemple, il peut simuler des avertissements légaux concernant des logiciels sans licence dans certaines régions ou se faire passer pour des forces de l'ordre ailleurs, exiger une rançon pour un contenu présumé illégal trouvé sur l'ordinateur.
How to Check Whether Win64:Malware-gen Is Real
Identifier une infection par un logiciel malveillant implique de noter les ralentissements soudains de l'ordinateur, processus inconnus, activités étranges du navigateur, alertes antivirus sur les menaces indétectables, problèmes d'application, l'écran scintille, ou des arrêts inattendus.
Quels sont les effets négatifs de Win64:Génération de logiciels malveillants?
Les ordinateurs infectés peuvent rencontrer:
- Installations de logiciels malveillants supplémentaires.
- Fausses fenêtres contextuelles de mise à jour ou d'installation de programmes.
- Engagement dans la fraude au clic.
- Inclusion dans la distribution de spam ou dans les botnets.
- Accès des pirates à distance pour le vol de données, y compris les frappes au clavier, visites de sites Web, et informations sensibles via les modifications du registre.
- Bombardements de publicités sur Internet.
- Conversion du texte d'une page Web en hyperliens.
- Le vol de données sensibles conduit à des transactions frauduleuses, vol d'identité, et pertes financières.
Win64:La génération de logiciels malveillants constitue une menace importante, non seulement en perturbant les fonctionnalités des appareils personnels, mais aussi en mettant les utilisateurs en danger’ sécurité financière et personnelle.
Win64:Variantes de génération de logiciels malveillants
| Antivirus | Détection |
|---|---|
| Centre de sécurité du cloud Alibaba | Cheval de Troie Dropper:Win64/LaZagne.8fcc6442 |
| Avast | Win64:Génération de logiciels malveillants |
| MOYENNE | Win64:Génération de logiciels malveillants |
| Avira | HEUR/AGEN.1046641 |
| Bitdefender | Cheval de Troie.PasswordStealer.GenericKDS.33544129 |
| la toile | Cheval de Troie.Siggen9.20767 |
| Emsisoft | Cheval de Troie.GenericKD.33545160 (B) |
| Oeil de feu | Générique.mg.d08c3a2f1f530dcb |
| F-Secure | Heuristic.HEUR/AGEN.1046641 |
| GridinSoft | Trojan.Ransom.Gen |
| K7GW | Logiciels à risques ( 0040eff71 ) |
| Kaspersky | pas un virus:HEUR:PSWTool.Python.LaZagne.gen |
| McAfee | Artémis!D08C3A2F1F53 |
| McAfee GW édition | Se comporte comme.Win32.Backdoor.vc |
| Microsoft | troyen:Win32/Occamy.C |
| Qihoo 360 | HEUR/QVM10.1.E9CF.Malware.Gen |
| Sophos | PUA KE générique (PUA) |
| Symantec | Cheval de Troie.Gen.MBT |
| Tendance Micro Apex One | Mal intentionné |
| TrendMicro HouseCall | TROJ_GEN.R002H07CE20 |
How to Remove Win64:Malware-gen Safely
Compte tenu de sa sophistication, la détection et la suppression de Malware-Gen exigent le plus grand soin. Ce virus connu pour gêner l'exécution des logiciels de sécurité, vous oblige à contourner ces restrictions pour réussir la suppression et la récupération du système.
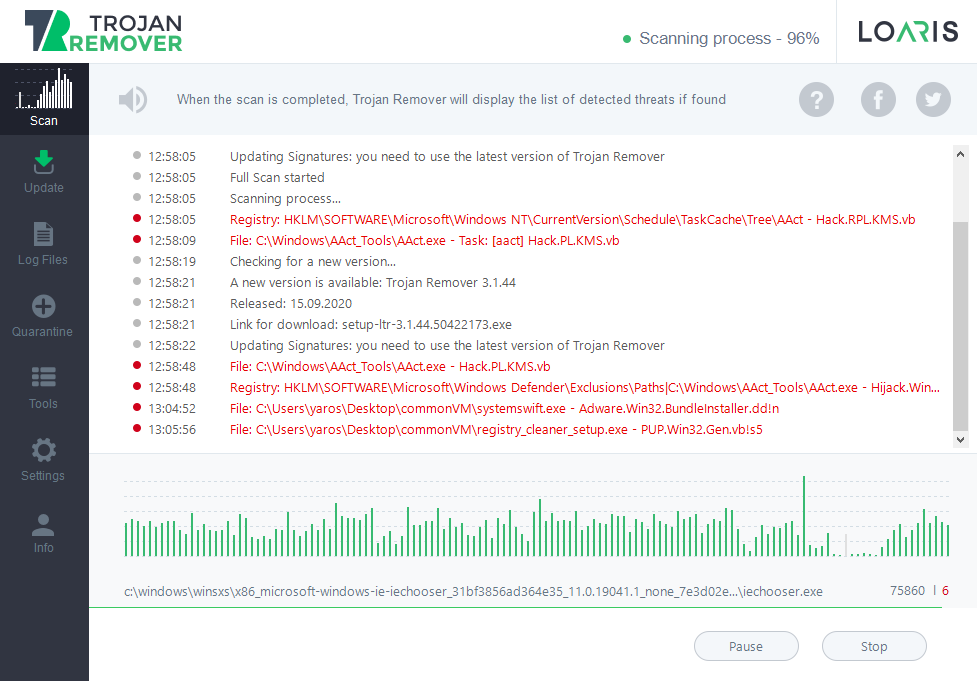
Loaris Trojan Remover se distingue comme le premier choix pour éradiquer la menace Win64 Malware-gen et restaurer votre système. Il dispose d'un moteur d'analyse avancé qui détecte les logiciels malveillants sous toutes leurs formes et permet des analyses ciblées grâce à sa fonction d'analyse personnalisée..
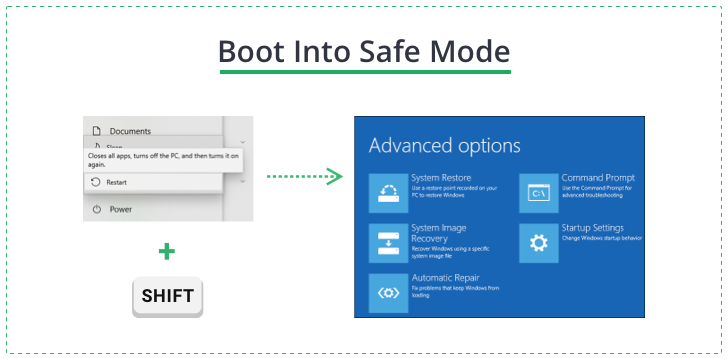
Pour naviguer dans les blocs d’exécution du ransomware, démarrez votre PC dans Mode sans échec avec réseau. Cela peut être fait via le panneau de dépannage en redémarrant votre PC tout en maintenant la touche Maj enfoncée., accéder aux paramètres de démarrage, et en sélectionnant Windows 10 Mode sans échec avec réseau.
En mode sans échec, lancez l'installateur de Loaris, suivez les instructions d'installation, et activez l'essai gratuit pour bénéficier de toutes les fonctionnalités.
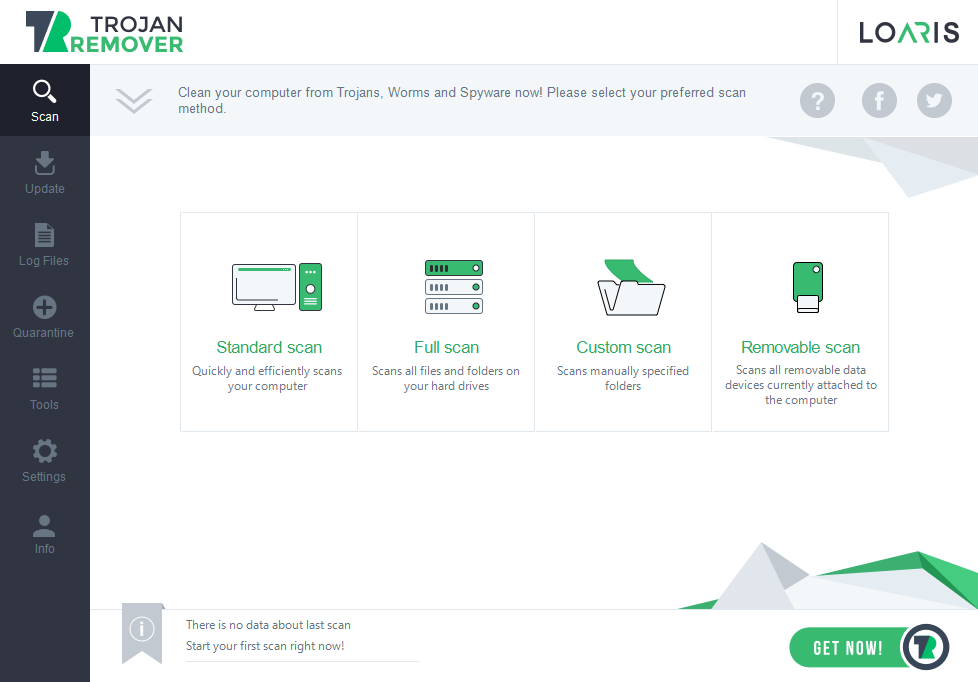
Effectuer une analyse complète, consulter la liste des menaces détectées, et procédez aux actions de suppression recommandées.