Trojan:O97M/Madeba!pz er en type ondsindet software, almindeligvis kendt som en trojaner, der er rettet mod Microsoft Office-dokumenter. Helt konkret, det påvirker filer, der er oprettet med ældre versioner af Microsoft Office, såsom Office 97-2003 (.dok, .xls, .ppt filer).
Trojanske heste som Madeba!pz fungerer typisk ved at udnytte sårbarheder i Office-pakken til at udføre skadelig kode, når det inficerede dokument åbnes. Når den er aktiveret, de kan udføre forskellige skadelige handlinger, såsom at stjæle følsomme oplysninger, kompromittere systemsikkerheden, eller installere yderligere malware på den inficerede computer.
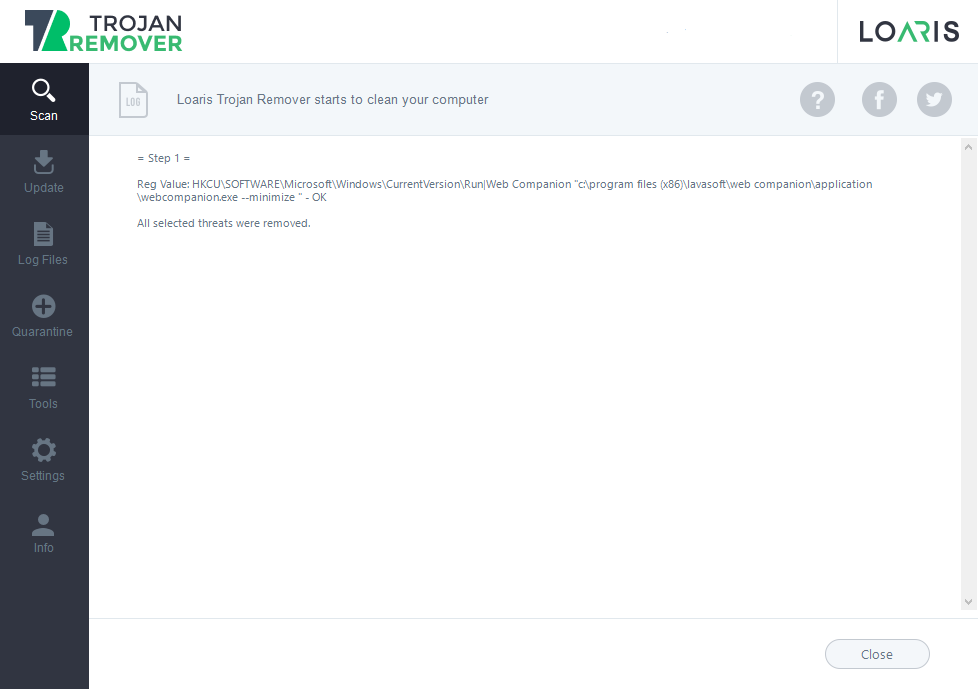
Trojan:Win32/Casdet!rfn i aktion

Trojan:O97M/Madeba!pz kan injiceres i en Windows-pc gennem forskellige metoder, primært udnyttelse af sårbarheder i software eller gennem social engineering taktik. Her er en analyse af potentielle måder, det kan inficere dit system på:
- E-mail-vedhæftede filer: En almindelig metode er gennem ondsindede vedhæftede filer. Angribere kan sende e-mails, der foregiver at være fra legitime kilder, såsom en kollega, ven, eller betroet organisation. Disse e-mails indeholder ofte vedhæftede filer, der virker harmløse, såsom Word-dokumenter, Excel regneark, eller PowerPoint-præsentationer. Imidlertid, disse filer indeholder ondsindede makroer eller scripts, der, når den henrettes, download og kør trojaneren på dit system.
- Drive-by-downloads: En anden metode involverer drive-by downloads, hvor trojaneren i ro og mag downloades og installeres på dit system, når du besøger et kompromitteret eller ondsindet websted. Disse websteder udnytter sårbarheder i din browser eller browser-plugins til at udføre ondsindet kode uden din viden.
- Inficerede eksterne enheder: Trojan:O97M/Madeba!pz kan også spredes gennem inficerede eksterne enheder såsom USB-drev, eksterne harddiske, eller endda smartphones. Når du tilslutter en inficeret enhed til din pc, trojaneren kan automatisk udføre og inficere dit system.
- Udnyttelse af softwaresårbarheder: Trojan:O97M/Madeba!pz udnytter ofte sårbarheder i softwareapplikationer for at få uautoriseret adgang til dit system. Dette kan omfatte sårbarheder i Microsoft Office, webbrowsere, eller anden almindeligt anvendt software. Angribere udnytter disse sårbarheder ved at lave specialdesignede dokumenter eller filer, der, når den åbnes, udløse eksekvering af ondsindet kode.
- Social Engineering: Angribere kan bruge social engineering-taktik til at narre dig til manuelt at downloade og udføre trojaneren. For eksempel, de kan skabe falske websteder eller reklamer, der hævder at tilbyde gratis software, spil, eller medieindhold. Når du downloader og kører disse filer, du utilsigtet installerer trojaneren på dit system.
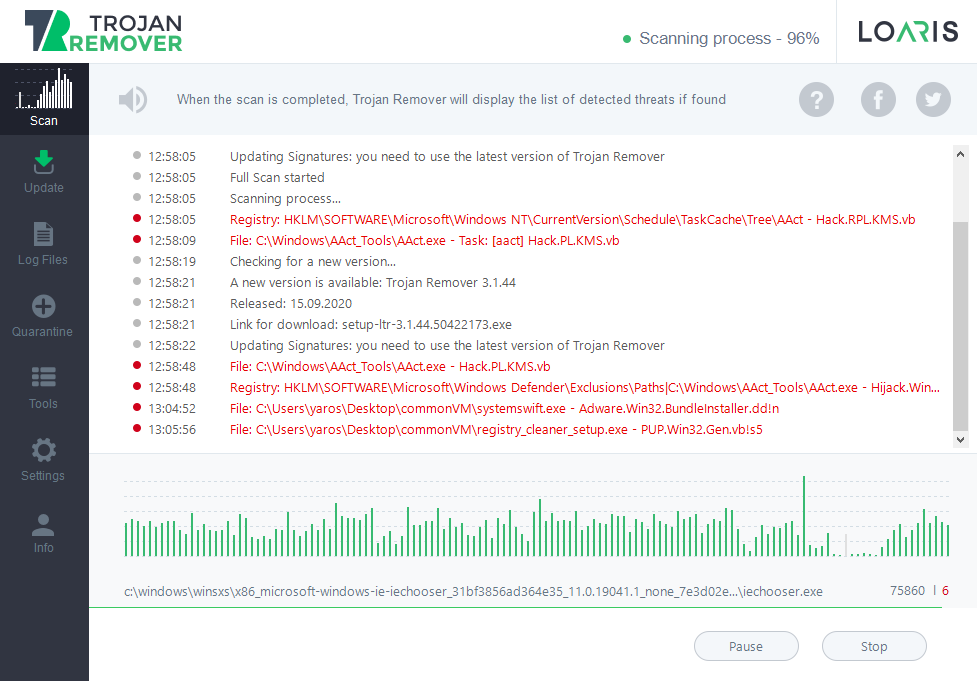
Trojan:O97M/Madeba!pz leveres til ofrets system gennem en af de tidligere nævnte metoder, såsom vedhæftede filer i e-mails, drive-by downloads, inficerede eksterne enheder, eller udnyttelse af softwaresårbarheder.
Når den skadelige fil er åbnet eller udført, trojanerens kode er aktiveret. Dette kan involvere udnyttelse af sårbarheder i softwareapplikationer, udførelse af ondsindede makroer i Microsoft Office-dokumenter, eller udnyttelse af andre midler til at udføre sin nyttelast.
Trojan Madeba persistens på det inficerede system for at sikre, at det forbliver aktivt, selv efter systemet genstarter. Det kan opnå dette ved at oprette registreringsposter, ændring af systemfiler, eller installere sig selv som en service eller et startprogram.
Efter at have etableret persistens, trojaneren udfører sin nyttelast. Denne nyttelast kan omfatte forskellige ondsindede aktiviteter, såsom at stjæle følsomme oplysninger, logge tastetryk, optagelse af skærmbilleder, kryptering af filer til løsesum, eller omdanne det inficerede system til en bot til brug i et botnet.
Det kan forsøge at kommunikere med fjernkommando-og-kontrol (C&C) servere, der drives af angriberne. Denne kommunikation gør det muligt for angriberne at sende kommandoer til det inficerede system, hente stjålne data, eller opdatere trojaneren med nye instruktioner eller nyttelast.
Trojan:O97M/Madeba!pz anvender unddragelsesteknikker for at undgå opdagelse af antivirus- eller sikkerhedssoftware. Dette kan omfatte polymorf kode, der ændrer dens udseende med hver infektion, sløringsteknikker for at skjule dets sande formål, eller anti-analyseforanstaltninger for at forhindre reverse engineering forsøg.
Trojan:O97M/Madeba!pz kan spredes til andre systemer på netværket eller via flytbare drev. De forsøger at udnytte sårbarheder i netværkstjenester eller bruger social engineering taktik til at narre brugere på det samme netværk til at udføre malwaren. Det sletter logs, ændrer systemfiler, eller på anden måde forsøger at skjule sin tilstedeværelse på det inficerede system.
Trojan:O97M/Madeba!pz Resumé
Trojan:Win32/Casdet!rfn anvender sofistikerede teknikker til at undgå påvisning og analyse. Disse omfatter: